Blog
CPA AI Policy Template: Free Download for Canadian Accounting Firms
CPA AI Policy Template: Free Download for
CCH iFirm and CaseWare Cybersecurity Hardening for Canadian Accounting Firms (2026)
Written by Mike Pearlstein, CISSP, MSc AI, CEO
Microsoft 365 Copilot vs Generic ChatGPT for Canadian CPA Firms (2026)
Written by Mike Pearlstein, CISSP, CEO of Fusion
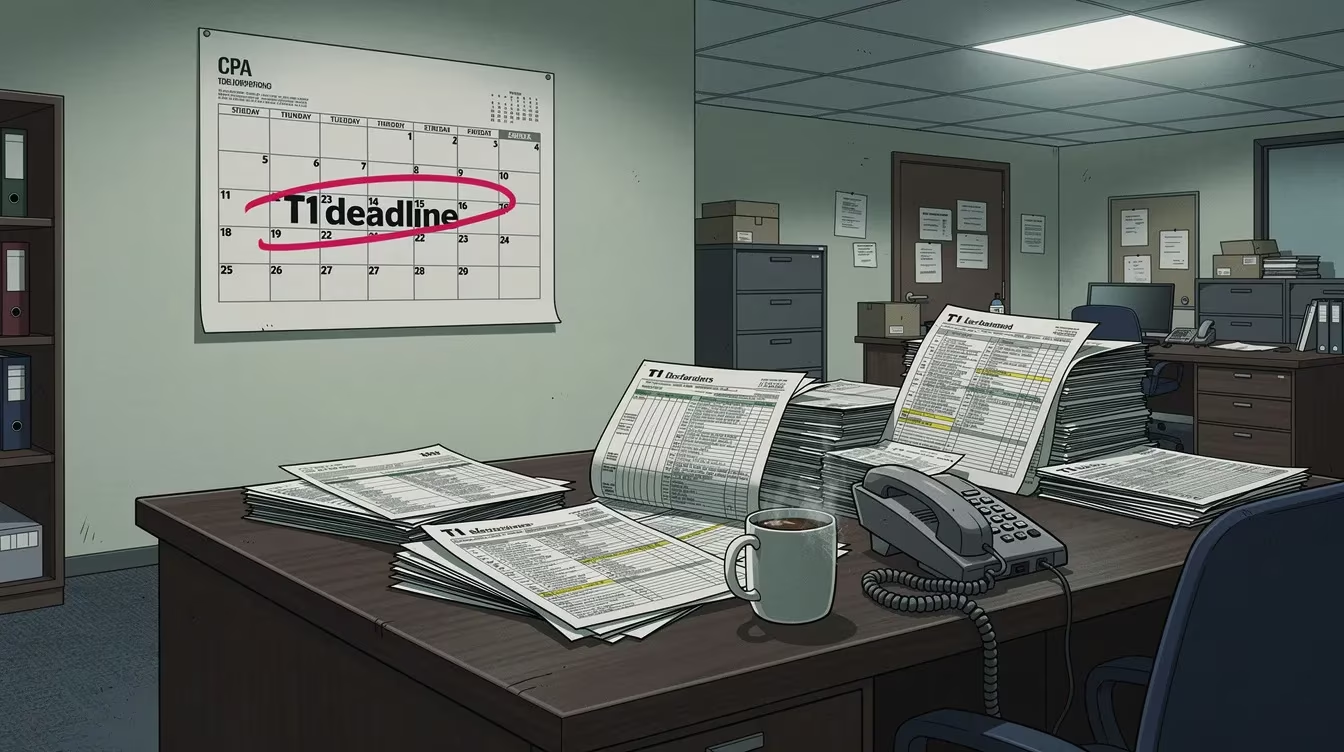
Tax-Season Cybersecurity for Canadian CPA Firms: A First-Hand Playbook for 2026
Tax-Season Cybersecurity for Canadian CPA Firms: A First-Hand Playbook for 2026 Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses
FINTRAC IT Controls for Canadian Accountants: A 2026 Practitioner Guide
Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton,
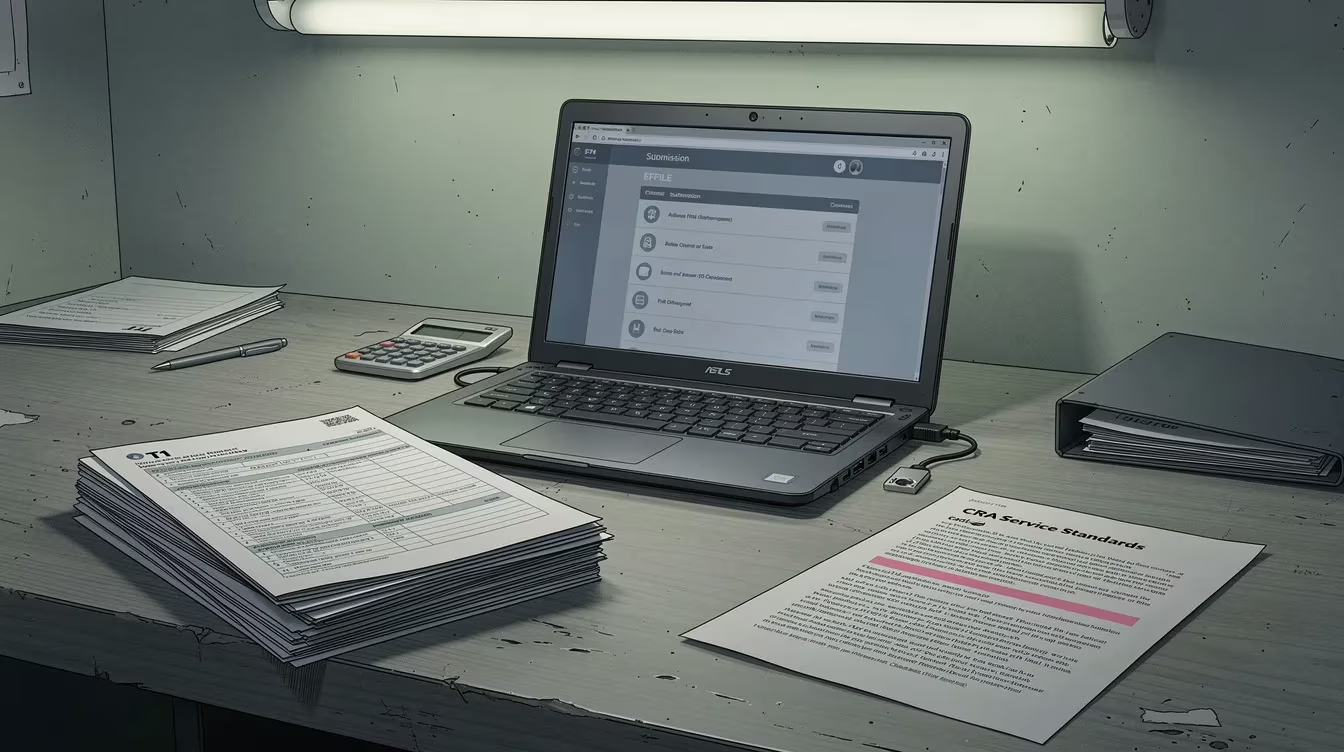
CRA EFILE Security for Canadian Accounting Firms: A 2026 Compliance and Hardening Guide
CRA EFILE Security for Canadian Accounting Firms: A 2026 Compliance and Hardening Guide Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping

Microsoft Purview for Ontario Healthcare Clinics: A PHIPA-Compliant eDiscovery and Legal Hold Walkthrough (2026)
Microsoft Purview for Ontario Healthcare Clinics: A PHIPA-Compliant eDiscovery and Legal Hold Walkthrough (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited.
AI for Ontario Insurance Brokerages: A Pre-FSRA-Rules Compliance Roadmap for 2026
AI for Ontario Insurance Brokerages: A Pre-FSRA-Rules Compliance Roadmap for 2026 Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses
Filogix and Velocity Account Hardening for Canadian Mortgage Brokers (2026)
Written by Mike Pearlstein, CISSP, MSc AI, CEO of Fusion Computing Limited. Helping Canadian mortgage brokerages and financial-services firms build and manage secure IT
The 875K FSRA Mortgage Brokerage Penalty: What 2025-26 Enforcement Means for Your Cybersecurity Plan
The $875K FSRA Mortgage Brokerage Penalty: What 2025-26 Enforcement Means for Your Cybersecurity Plan Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited.
RIBO Responsible AI Use: A 4-Pillar Policy Template for Ontario Insurance Brokerages (2026)
RIBO Responsible AI Use: A 4-Pillar Policy Template for Ontario Insurance Brokerages (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping
MBRCC’s Cybersecurity Principles Decomposed Into 9 Controls for a 12-Agent Ontario Mortgage Brokerage (2026)
MBRCC's 4 Cybersecurity Principles, Decomposed Into 9 Controls for a 12-Agent Ontario Mortgage Brokerage (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing
FSRA IT Risk Incident Notification Form: A 15-Minute SOP for Ontario Brokerages (2026)
Cross-Border PHI in 2026: Why US-Hosted EMR Add-Ons Trigger Law 25 and CLOUD Act Exposure for Ontario Clinics
Cross-Border PHI in 2026: Why US-Hosted EMR Add-Ons Trigger Law 25 and CLOUD Act Exposure for Ontario Clinics Written by Mike Pearlstein, CISSP, CEO
CPSO AI Disclosure to Patients: When, How, and What to Document (2026)
CPSO AI Disclosure to Patients: When, How, and What to Document (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian
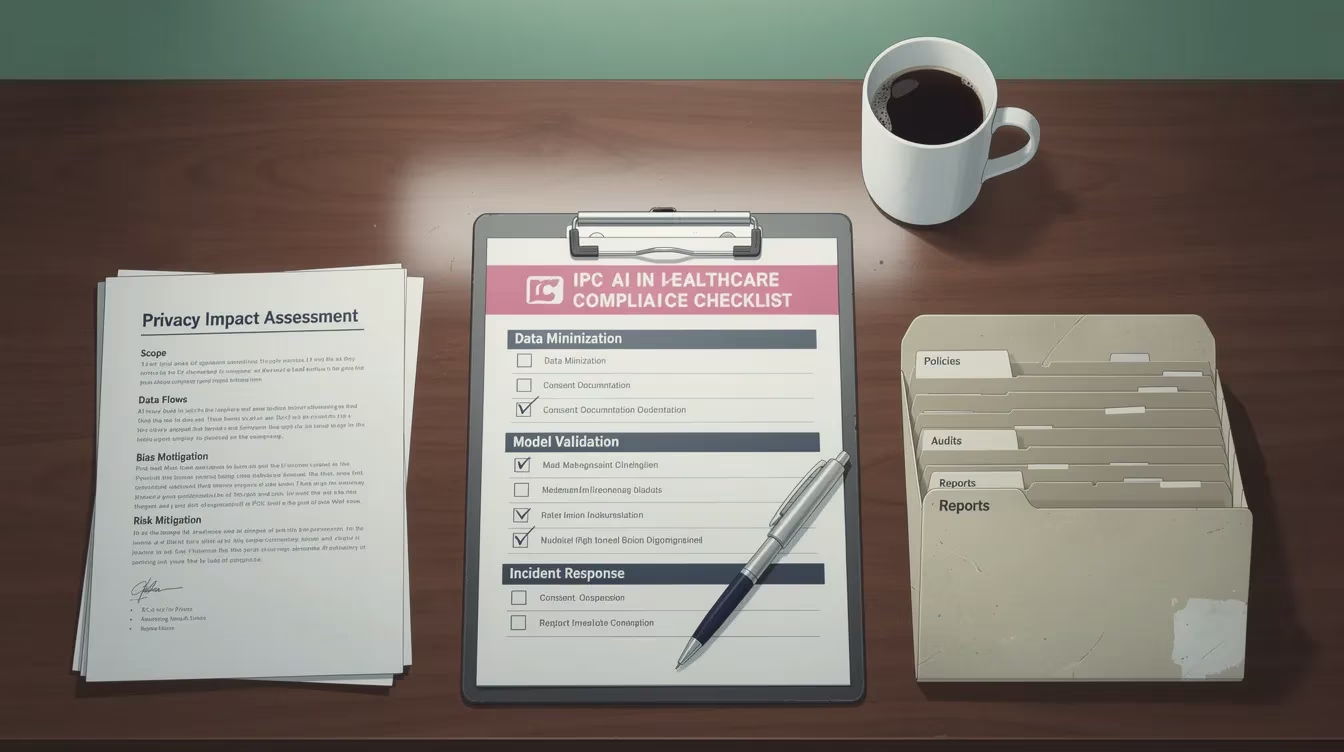
Applying the IPC’s AI-in-Healthcare Checklist: A 4-Doctor Clinic Walk-Through (2026)
Applying the IPC’s AI-in-Healthcare Checklist: A 4-Doctor Clinic Walk-Through (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build
OHIP Billing Data Security: The Clinic Owner’s 2026 Hardening Checklist
OHIP Billing Data Security: The Clinic Owner’s 2026 Hardening Checklist Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build
Ransomware Playbook for a 4-Physician FHO Clinic (PHIPA + CPSO Edition, 2026)
Ransomware Playbook for a 4-Physician FHO Clinic (PHIPA + CPSO Edition, 2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian
The 60-Day PHIPA Breach Notification SOP for Ontario Clinics (2026)
The 60-Day PHIPA Breach Notification SOP for Ontario Clinics (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build

AI Scribes for Ontario Family Doctors: A PHIPA-Safe Vendor Comparison (2026)

Cybersecurity for Ontario Financial Brokerages: An FSRA-Aligned MBRCC + RIBO Playbook for 2026
Cybersecurity for Ontario Financial Brokerages: An FSRA-Aligned MBRCC + RIBO Playbook for 2026 Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping
AI for Canadian Law Firms: A Privilege-Safe Deployment Guide for 2026
CPA AI Policy Template: Free Download for Canadian Accounting Firms
CPA AI Policy Template: Free Download for Canadian Accounting Firms Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses

CCH iFirm and CaseWare Cybersecurity Hardening for Canadian Accounting Firms (2026)
Written by Mike Pearlstein, CISSP, MSc AI, CEO of Fusion Computing Limited. Helping Canadian accounting firms and CPA practices build and manage secure IT
Microsoft 365 Copilot vs Generic ChatGPT for Canadian CPA Firms (2026)
Tax-Season Cybersecurity for Canadian CPA Firms: A First-Hand Playbook for 2026
FINTRAC IT Controls for Canadian Accountants: A 2026 Practitioner Guide
CRA EFILE Security for Canadian Accounting Firms: A 2026 Compliance and Hardening Guide

Microsoft Purview for Ontario Healthcare Clinics: A PHIPA-Compliant eDiscovery and Legal Hold Walkthrough (2026)
AI for Ontario Insurance Brokerages: A Pre-FSRA-Rules Compliance Roadmap for 2026
Filogix and Velocity Account Hardening for Canadian Mortgage Brokers (2026)
The 875K FSRA Mortgage Brokerage Penalty: What 2025-26 Enforcement Means for Your Cybersecurity Plan
RIBO Responsible AI Use: A 4-Pillar Policy Template for Ontario Insurance Brokerages (2026)
MBRCC’s Cybersecurity Principles Decomposed Into 9 Controls for a 12-Agent Ontario Mortgage Brokerage (2026)
FSRA IT Risk Incident Notification Form: A 15-Minute SOP for Ontario Brokerages (2026)
Cross-Border PHI in 2026: Why US-Hosted EMR Add-Ons Trigger Law 25 and CLOUD Act Exposure for Ontario Clinics
CPSO AI Disclosure to Patients: When, How, and What to Document (2026)
Applying the IPC’s AI-in-Healthcare Checklist: A 4-Doctor Clinic Walk-Through (2026)
OHIP Billing Data Security: The Clinic Owner’s 2026 Hardening Checklist
Newsletter
Get our latest content delivered to your inbox.
Related Resources
- managed IT services Toronto
- managed IT services Hamilton
- managed IT services Vancouver
- managed IT services
- cybersecurity services
- IT support

