In 2023, one in five Canadian businesses experienced a cybersecurity incident, according to Statistics Canada. The majority of those incidents exploited weaknesses in IT infrastructure: unpatched servers, misconfigured firewalls, exposed remote access points, and flat networks that let attackers move freely once inside.
Infrastructure security isn’t a product you buy. It’s a discipline: a set of layered controls that protect the hardware, software, networks, and data your business runs on. For Canadian SMBs, getting infrastructure security right is the difference between operating with confidence and operating on borrowed time.
This guide covers what IT infrastructure security actually means in practice, the controls that matter most for small and mid-size businesses, and a checklist you can use to evaluate where your organization stands today.
If you’re moving from checklist to implementation, use our cybersecurity services page for managed protection, our cybersecurity assessment Toronto page for scoped validation work, and our IT assessment page to map the gaps into a remediation plan.
KEY TAKEAWAYS
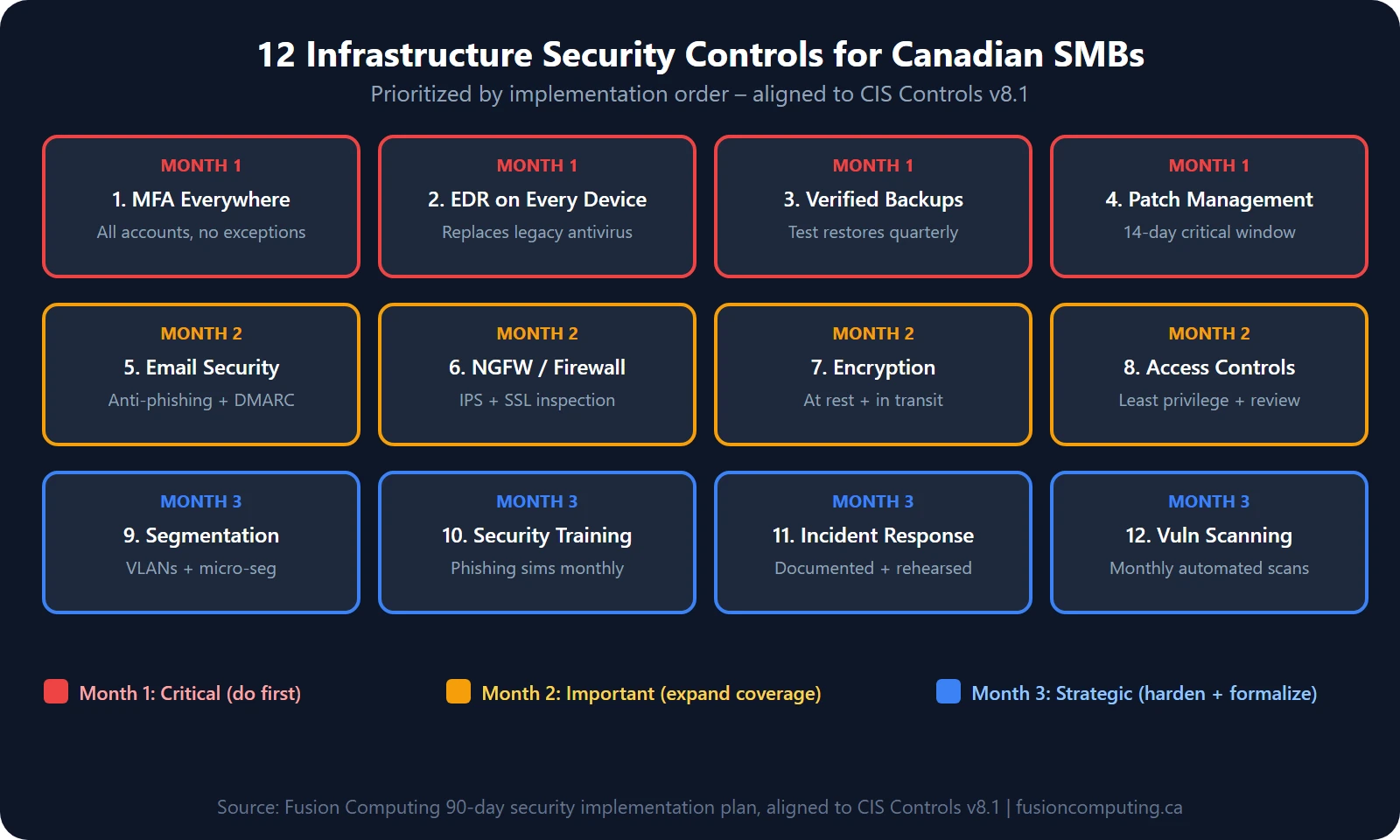
- Infrastructure security isn’t one product – it’s 12 controls working together: access, EDR, patching, backup, encryption, segmentation, and more.
- The average Canadian data breach costs CA$6.98 million (IBM, 2025). Most SMB breaches exploit basic gaps these 12 controls would have caught.
- Start with the 90-day plan: MFA + EDR + backup verification in month one. You don’t need to do everything at once.
- CIS Controls v8.1 is the framework – not a checklist you print and forget. Map it to your environment quarterly.
What is IT infrastructure security?
IT infrastructure security is the practice of protecting servers, networks, endpoints, cloud environments, and data storage from unauthorized access and cyber threats. The 6 core controls—network segmentation, endpoint detection and response (EDR), identity and access management with MFA, data encryption, vulnerability scanning, and 24/7 security monitoring—reduce breach risk by over 70% for Canadian SMBs.
TL;DR
IT infrastructure security protects the physical and virtual components of your technology environment—servers, networks, endpoints, cloud services, and data storage—from unauthorized access, data breaches, and service disruption. A comprehensive infrastructure security program includes network segmentation, endpoint protection, access controls, encryption, vulnerability scanning, and 24/7 monitoring.
IT infrastructure security is the practice of protecting the hardware, software, networks, and data that form the foundation of a business’s technology operations. For Canadian SMBs, this means implementing controls across 12 categories – from access management and endpoint detection to encryption and disaster recovery – aligned to frameworks like CIS Controls v8.1. The average Canadian breach costs CA$6.98 million (IBM, 2025).
IT infrastructure security refers to the policies, tools, and practices that protect the foundational technology systems a business depends on. This includes physical components (servers, networking equipment, endpoints), virtual systems (cloud platforms, virtual machines, containers), software (operating systems, applications, databases), network architecture (firewalls, switches, wireless access points, VPNs), and data stores (file servers, cloud storage, backups).
Fusion Computing is a CISSP-certified managed security services provider (MSSP) serving Canadian businesses since 2012. All security operations align to CIS Controls v8.1, with 24/7 managed detection and response, endpoint protection, and incident response — delivered from Canadian offices with all data stored in Canada.
Infrastructure security is broader than cybersecurity, which focuses primarily on defending against external threats. Infrastructure security also covers internal risks, physical access, redundancy, disaster recovery, and the architecture decisions that determine how resilient your environment is when something goes wrong.
| Infrastructure Security vs. Cybersecurity vs. Network Security: How They Relate
Infrastructure security is the broadest category. It covers physical, virtual, and process-based protection for all IT systems. Cybersecurity focuses specifically on defending against digital threats (malware, phishing, ransomware, data breaches). Network security is a subset that protects the communication pathways between systems. All three overlap, but infrastructure security is the foundation that the other two build on. |
Why Infrastructure Security Matters for Canadian SMBs
Infrastructure security is the practice of protecting an organization’s core IT systems—servers, networks, endpoints, cloud environments, and data storage—from unauthorized access, disruption, and data loss. It includes firewalls, intrusion detection, access controls, encryption, patch management, and physical security. Strong infrastructure security forms the foundation for all other cybersecurity efforts.
The average cost of a data breach in Canada reached $4.44 million in 2025 according to the IBM Cost of a Data Breach Report. For small businesses, even a fraction of that figure can be devastating. Lost revenue during downtime, legal exposure from compromised customer data, regulatory penalties under PIPEDA, and reputational damage that takes years to rebuild.
Canadian SMBs face specific infrastructure security challenges that enterprise-focused guides overlook. Most run hybrid environments with a mix of on-premises and cloud infrastructure that evolved organically rather than by design. Many rely on aging hardware that has passed end-of-life and no longer receives security patches. Remote and hybrid work expanded the attack surface without corresponding investment in secure access. And budget constraints mean security investments compete directly with revenue-generating projects.
The good news is that infrastructure security doesn’t require an enterprise budget. It requires the right priorities, the right architecture decisions, and consistent execution of fundamentals.
IT Infrastructure Security Checklist: 12 Essential Controls
1. Maintain a Complete Asset Inventory
You can’t protect what you don’t know exists. Maintain a current inventory of every device, server, application, and cloud service in your environment. Include hardware model, software version, patch level, owner, and network location. Review the inventory quarterly and update it whenever changes occur.
Shadow IT, meaning applications and services adopted by employees without IT approval, is one of the most common infrastructure security gaps. A 2024 Gartner survey found that 41 percent of employees use technology their IT department doesn’t know about.
2. Segment Your Network
A flat network where every device can communicate with every other device is an attacker’s dream. Network segmentation divides your environment into isolated zones so that a compromised endpoint in accounting can’t reach the database server or the backup infrastructure.
At minimum, segment your network into trust zones: a user network for employee workstations, a server network for critical infrastructure, a guest or IoT network for untrusted devices, and a management network for administrative access to infrastructure components. Use VLANs and firewall rules to enforce boundaries between zones.
3. Patch and Update Everything
Unpatched systems are the number one entry point for attackers. Establish a patch management process that applies critical security patches within 72 hours of release and all other patches within 30 days. This applies to operating systems, firmware, applications, and network devices, not just Windows endpoints.
End-of-life hardware and software that no longer receives patches must be replaced or isolated. Running a Windows Server 2012 instance in production in 2026 isn’t a budget decision. It’s an unmanaged risk.
4. Implement Layered Access Controls
Every system should enforce the principle of least privilege: users get only the access they need to do their job, and no more. Implement multi-factor authentication on every external-facing system and all privileged accounts. Use role-based access control (RBAC) to manage permissions systematically rather than granting access ad hoc.
Review access quarterly. When employees change roles or leave the company, their access should be adjusted immediately, not months later when someone notices.
5. Deploy Endpoint Detection and Response (EDR)
Traditional antivirus is no longer sufficient. EDR solutions monitor endpoint behaviour in real time, detect suspicious activity that signature-based tools miss, and enable rapid containment when a threat is identified. EDR should be deployed on every endpoint (servers, workstations, and laptops) with centralized monitoring and alerting.
6. Secure Your Perimeter (and Assume It Will Be Breached)
Next-generation firewalls, intrusion detection and prevention systems (IDS/IPS), and DNS filtering form the perimeter defence layer. But modern infrastructure security assumes the perimeter will be breached and builds internal defences accordingly. This is the zero trust security approach: verify every user, every device, and every connection regardless of whether it originates inside or outside the network.
7. Encrypt Data at Rest and in Transit
Data encryption protects information even if an attacker gains access to your systems. Encrypt data at rest on servers, endpoints, and backup media using AES-256 or equivalent. Encrypt data in transit using TLS 1.2 or higher for all internal and external communications. Pay special attention to backup data. An unencrypted backup is a goldmine for an attacker.
8. Implement Backup and Disaster Recovery
Infrastructure security includes resilience, the ability to recover when something goes wrong. Follow the 3-2-1 backup rule: three copies of critical data, on two different media types, with one copy stored offsite or in the cloud. Test restores regularly. A backup that has never been tested isn’t a backup.
Define recovery time objectives (RTO) and recovery point objectives (RPO) for each critical system. How long can the business survive without email? Without the ERP system? Without file access? The answers determine your backup frequency and recovery architecture.
9. Monitor and Log Everything
Security monitoring gives you visibility into what is happening across your infrastructure. Centralize logs from firewalls, servers, endpoints, and cloud services into a SIEM or log management platform. Set up alerts for anomalous behaviour: failed login attempts, privilege escalation, unusual data transfers, or access from unexpected locations.
Without monitoring, breaches go undetected for weeks or months. IBM reports that the average time to identify a breach in 2024 was 241 days (IBM Cost of a Data Breach Report, 2025). Continuous monitoring reduces that window dramatically.
10. Manage Vulnerabilities Proactively
Run vulnerability assessments at least quarterly and after any significant infrastructure change. Complement automated scans with periodic penetration testing that simulates real-world attack scenarios. Prioritize remediation based on exploitability and business impact, not just CVSS scores. Include network security testing to evaluate firewall rules, segmentation, and perimeter defenses.
11. Secure Cloud and Hybrid Infrastructure
Cloud infrastructure requires the same security rigour as on-premises systems, often more so because misconfigurations are the leading cause of cloud breaches. Audit cloud configurations against CIS Benchmarks. Enforce MFA on all cloud admin accounts. Monitor for publicly exposed storage buckets, databases, and API endpoints. Ensure your cloud migration includes a security architecture review, not just a lift-and-shift.
12. Train Your People
Technology controls fail when people circumvent them. Regular security awareness training reduces the risk of phishing, social engineering, and accidental data exposure. Training should be ongoing (not a once-a-year checkbox), relevant to each role, and reinforced with simulated phishing exercises.
Get a Free Infrastructure Assessment
Infrastructure Security on an SMB Budget
You don’t need to implement all 12 controls simultaneously. Prioritize based on risk and build your security posture over 90 days.
First 30 days (quick wins): Complete your asset inventory. Enable MFA everywhere it isn’t already active. Patch all critical vulnerabilities. Review and revoke unnecessary access.
Days 30 to 60 (foundation): Deploy EDR if not already in place. Implement network segmentation between user and server networks. Establish a patch management cadence. Test your backups.
Days 60 to 90 (maturity): Set up centralized logging and monitoring. Run your first vulnerability assessment and schedule network pen testing for critical systems. Document your incident response plan. Begin cloud security hardening.
This phased approach lets you address the highest-risk gaps first while building toward a mature security posture without overwhelming your budget or your team.
Book a Cybersecurity Assessment
Fusion Computing secures infrastructure across Toronto & GTA | Hamilton | Metro Vancouver
How Fusion Computing Secures Your Infrastructure
At Fusion Computing, infrastructure security is built into everything we do as a managed IT services provider. Our team includes CISSP-certified leadership that brings enterprise security discipline to SMB environments, without the enterprise price tag.
We start with a full cybersecurity assessment that maps your infrastructure, identifies gaps, and prioritizes remediation. Then we implement and manage the controls: EDR, SIEM, patch management, backup monitoring, and 24/7 alerting through our managed security services.
Whether you need a full security overhaul or a second opinion on your current posture, we can help.
Mike Pearlstein is CEO of Fusion Computing and holds the CISSP, the gold standard in cybersecurity certification. He has led Fusion’s managed IT and cybersecurity practice since 2012, serving Canadian businesses across Toronto, Hamilton, and Metro Vancouver.
At minimum, every business needs a next-generation firewall, endpoint detection and response (EDR) on all devices, multi-factor authentication on all external-facing systems, a tested backup and recovery solution, and a patch management process that addresses critical vulnerabilities within 72 hours. These five controls address the most common attack vectors and give you a defensible security baseline.
How much does it cost to secure IT infrastructure properly?
For a Canadian SMB with 25 to 100 employees, expect to invest $3,000 to $15,000 per month in managed security services that include EDR, SIEM monitoring, patch management, backup management, and security operations support. One-time costs for infrastructure upgrades (firewall replacement, network segmentation, cloud hardening) typically range from $10,000 to $50,000 depending on complexity. Compare that to the average breach cost of $5.13 million reported by IBM for Canadian organizations.
What is the difference between infrastructure security and cybersecurity?
Infrastructure security is the broader discipline that covers all protections for IT systems: physical security, network architecture, redundancy, disaster recovery, and access controls. Cybersecurity is a subset focused specifically on defending against digital threats like malware, ransomware, phishing, and data exfiltration. You can’t have effective cybersecurity without solid infrastructure security as the foundation.
Can we manage infrastructure security with an MSP instead of hiring in-house?
Yes, and for most SMBs this is the more cost-effective and capable approach. A qualified MSP or MSSP provides 24/7 monitoring, faster incident response, and access to security tools and expertise that would cost $200,000 or more per year to build internally. The key is choosing a provider with demonstrated security credentials (look for CISSP, SOC 2, or equivalent certifications) rather than a generalist IT company that bolts on security as an afterthought.
What should be in an infrastructure security audit?
A thorough infrastructure security audit covers asset inventory and classification, network architecture and segmentation review, firewall and access control configuration, patch and vulnerability status, endpoint protection coverage, backup and disaster recovery testing, cloud configuration assessment, user access review, physical security controls, and compliance gap analysis against frameworks like CIS Controls v8 or NIST CSF. The audit should produce a prioritized remediation plan with timelines and estimated costs.
Fusion Computing serves Canadian businesses across:
Cybersecurity Services — Toronto · Cybersecurity Services — Hamilton · Cybersecurity Services — Vancouver


