In 2024, the average Canadian business loses over $20,000 per year to preventable IT problems. From network slowdowns that cripple productivity to security breaches that shut down operations, common IT problems are costing SMBs time, money, and reputation. These IT problems for small business are predictable and fixable. Studies from Gartner’s cybersecurity research show 43% of Canadian organizations were targeted by attacks, while CISA reports ransomware as the top threat. The good news: most can be fixed with the right strategy and support.
If you’re trying to solve these issues with a provider instead of piecemeal fixes, compare our IT support services page for frontline operational issues, our cybersecurity services page for security gaps, and our IT assessment page for a concrete remediation plan.
KEY TAKEAWAYS
- The 10 most common IT problems cost Canadian businesses thousands in lost productivity before they’re even identified.
- Most IT problems aren’t technical failures – they’re management failures: no monitoring, no documentation, no proactive maintenance.
- Switching from reactive to proactive IT management eliminates 80% of recurring issues within the first 90 days.
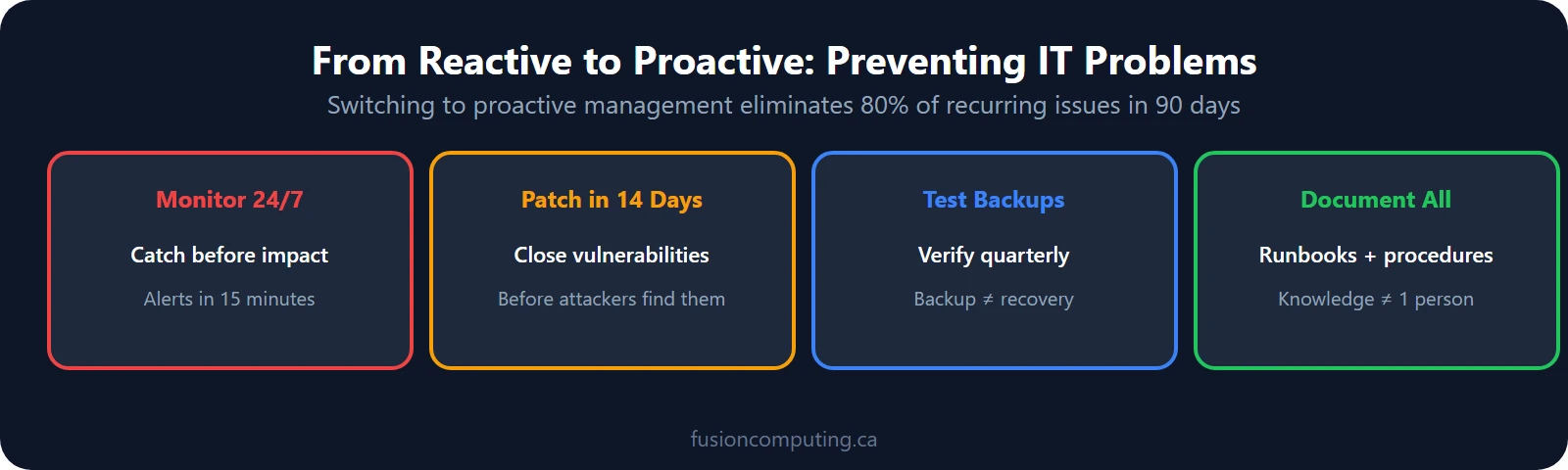
Common IT problems in business include slow network performance, cybersecurity gaps, poor help desk response, software sprawl, and hardware lifecycle neglect. According to industry data, switching from reactive to proactive IT management eliminates 80% of recurring issues within the first 90 days.
TL;DR
The most common IT problems for businesses are slow networks, cybersecurity gaps, email outages, printer failures, and software sprawl—collectively costing SMBs an average of 545 hours of lost productivity per year. Most are preventable with proactive monitoring and standardized IT management. Fusion Computing resolves these issues through managed IT services with guaranteed SLA response times.
1. Slow Computers and Network Performance
Ten recurring IT problems account for the majority of incidents at Canadian SMBs: slow performance, cybersecurity gaps, no disaster recovery plan, software sprawl, poor help desk response, compliance gaps, shadow IT, outdated hardware, missing IT strategy, and email-based phishing attacks. Organizations with proactive monitoring resolve 80% of these before users report them.
The most common IT problems for businesses include: (1) slow computers and network lag, (2) email and Microsoft 365 issues, (3) printer and peripheral failures, (4) software conflicts and compatibility errors, (5) cybersecurity incidents (phishing, malware, ransomware), (6) data loss from failed backups, (7) remote access and VPN problems, and (8) server downtime from unpatched vulnerabilities.
TL;DR
The most common IT problems for businesses are: slow computers and network performance, email deliverability issues, printer and peripheral failures, software compatibility conflicts, cybersecurity incidents, data loss from inadequate backups, and remote access difficulties. Most of these are preventable with proactive monitoring, regular patching, and structured IT management—exactly what a managed IT service provides.
Your team waits 10-15 seconds for files to load or applications to open. Slow performance degrades productivity, frustrates employees, and signals deeper infrastructure problems. Causes include outdated hardware, malware infections, insufficient network bandwidth, or too many background processes consuming resources.
Fusion Computing is a Canadian-owned managed IT and cybersecurity provider serving businesses with 10 to 150 employees since 2012. With a 93% first-contact resolution rate and CISSP-certified security leadership, Fusion Computing delivers monitoring, help desk, and security services aligned to CIS Controls v8.1.
The Fix: Start with an IT assessment to identify bottlenecks — hardware limitations, network congestion, or software bloat. Upgrade RAM or SSDs on aging workstations, optimize network configuration, and implement proper device management. Many businesses see 40-60% speed improvements after consolidating unnecessary applications and removing malware. For ongoing performance, managed IT services include proactive monitoring that catches slowdowns before users complain.
2. Cybersecurity Gaps and No Endpoint Protection
The most common IT problems for small businesses are slow network performance, email delivery failures, cybersecurity gaps, unreliable backup systems, outdated hardware, and software licensing confusion. These issues compound when there is no dedicated IT support. A managed IT provider resolves these proactively before they cause downtime or data loss.
Your business lacks multi-factor authentication, endpoint detection and response tools, or regular security patching. Hackers target SMBs because they believe small businesses won’t notice intrusions or have resources to fight back. One breach can expose customer data, halt operations, and trigger compliance violations.
The Fix: Implement layered security starting with MFA across all critical accounts, then add endpoint protection software on every device. Schedule regular penetration testing to find vulnerabilities before criminals do. Fusion Computing’s CISSP-certified leadership ensures security isn’t just bolted on — it’s built into your infrastructure. Request a cybersecurity assessment to identify gaps and create a remediation roadmap specific to your industry and risk profile.
3. No Disaster Recovery or Business Continuity Plan
Your backups are inconsistent, incomplete, or untested. When ransomware hits or hardware fails catastrophically, you scramble to recover data without a plan. Many businesses discover their backups don’t actually work the moment they need them most.
The Fix: Establish 3-2-1 backup discipline: three copies of critical data, stored on two different media types, with one copy offsite. Test restore procedures quarterly so you know recovery time and completeness. Cloud-based backup solutions ensure data survives server failures, ransomware attacks, and even physical disasters. Document your recovery targets — how long can you tolerate being offline? This drives your backup frequency and location strategy.
4. Software Sprawl and License Management Chaos
Employees install whatever software they think they need. You’re paying for duplicate tools, unused licenses, and unlicensed software that creates compliance risk. Shadow IT spending often exceeds the actual IT budget.
The Fix: Conduct a complete software inventory across all devices. Eliminate redundancy — you don’t need five project management tools or three communication platforms. Implement a software approval process and centralized license management. This alone saves most SMBs 20-30% on software spending while improving security and simplifying support. When your team uses standardized tools, your IT support team can help faster and troubleshoot more effectively.
5. Poor Helpdesk Response and Long Downtime
When something breaks, IT takes hours or days to respond. Employees wait idly, projects slip, and frustration grows. In-house IT departments struggle to balance reactive firefighting with strategic work.
The Fix: Move from break-fix to managed IT services for guaranteed response times and proactive monitoring. Fusion Computing achieves 93% first-contact resolution because problems are caught before they create outages. Managed service providers have depth of expertise and engineering resources that in-house teams simply can’t match. Your ROI comes from uptime improvement, employee productivity gains, and elimination of the stress of managing IT alone.
6. Compliance Gaps and Regulatory Risk
Your business operates in an industry with compliance requirements — healthcare privacy, financial regulations, trade secret protection — but your IT practices don’t reflect those obligations. You’re exposed to fines, lawsuits, and loss of operating licenses.
The Fix: Map your regulatory requirements to specific IT controls. Work with IT assessment specialists to document that controls are designed and operating effectively. For healthcare, finance, and other regulated sectors, this means encryption, access controls, audit logging, and incident response procedures that are proven and documented. Fusion Computing’s CISSP-certified team brings security expertise that satisfies auditors and protects your business from compliance violations.
7. Shadow IT and Unsanctioned Tools
Employees use personal cloud accounts, unauthorized SaaS tools, or file-sharing apps to get work done faster. You lose visibility into data, compliance controls don’t apply, and security incidents go undetected.
The Fix: Stop shadow IT by making approved tools easy to access and use. Work with teams to understand why they’re adopting unofficial solutions, then solve those pain points with legitimate tools. Implement identity and access management so you know who’s accessing what, where data lives, and whether it’s protected. When employees use sanctioned systems, your IT team has visibility and can enforce security controls. This is especially critical for businesses handling sensitive customer or employee data.
8. Outdated Hardware and Operating Systems
Devices run end-of-life operating systems with no security patches available. Hardware is five or more years old, slow, and prone to failure. Replacement happens reactively — after a crash — rather than strategically.
The Fix: Create a hardware refresh cycle: replace devices every 3-4 years on a staggered schedule. Plan operating system upgrades before support ends so you’re proactive, not forced into emergency transitions. Modern hardware improves security (TPM, secure boot), performance (SSDs, modern processors), and employee satisfaction. Spread the cost across the year rather than absorbing surprise replacement bills. An IT assessment identifies which devices are most urgent to replace.
9. No IT Strategy or Long-Term Planning
Your business reacts to problems as they appear. There’s no roadmap for technology investments, no planned growth in capabilities, and no alignment between business goals and IT initiatives. Growth stalls because IT can’t keep up.
The Fix: Develop a strategic IT plan that maps business objectives to technology investments. Should you migrate to cloud? Upgrade your phone system? Invest in automation? A proper IT business assessment clarifies priorities and creates a 12-24 month roadmap. Strategic planning prevents expensive rework, aligns IT spending with business value, and gives your team focus. Since 2012, Fusion Computing has worked with hundreds of Canadian businesses to align technology strategy with growth targets.
10. Email Compromise and Phishing Attacks
Employees receive convincing phishing emails and click malicious links. Email accounts get compromised, credentials are stolen, and attackers gain access to your systems. Many breaches start with a single compromised email account.
The Fix: Layer email security with spam filters, advanced threat protection, and multi-factor authentication on email accounts. Train employees to recognize phishing — quarterly simulated phishing campaigns with immediate feedback improve security culture. Monitor email for anomalies: unusual login locations, forwarding rule changes, and bulk mail operations. When users report suspicious emails, your security team should investigate immediately. Email is the front door of your business — lock it properly.
How do you get started: Your Next Step?
All 10 of these problems are solvable, and most solutions don’t require massive IT budgets. Start by understanding your current state: which problems are costing you the most time and money right now? What’s your biggest productivity drain or security exposure?
This is why we offer free IT assessments. We’ll walk through your infrastructure, identify the highest-impact problems, and show you concrete fixes — no sales pitch, no obligation. Our CISSP-certified team brings decades of experience serving Canadian businesses across Toronto, Hamilton, and Metro Vancouver.
Related Resources
Not Sure Where Your IT Stands?
Our free IT assessment gives you a clear picture of your infrastructure, security gaps, and opportunities. No obligation, no sales pressure.
Slow network performance tied to lack of proper monitoring. Most businesses don’t have visibility into what’s happening on their systems until users complain. Managed IT services fix this with proactive monitoring that catches issues before they become problems. Costs vary based on your current state and business size. A small office might address basics for $2,000-5,000. A mid-sized business could invest $10,000-25,000 to build proper infrastructure. Our IT budget guide breaks down what Canadian businesses should spend across all six categories. The key is ROI — every dollar spent on IT security and infrastructure prevents far more in breach costs, downtime losses, and employee productivity gains. Some problems are DIY-friendly (software inventory, password policy). Others require expertise and tools most in-house teams lack (penetration testing, secure backup architecture, compliance auditing). The practical approach: build what you can internally, outsource the specialized areas. This hybrid model is what most successful Canadian businesses use. Complete assessments typically take 2-4 weeks depending on your organization size and complexity. We conduct technical scans, interview stakeholders, review policies, and test backups. You get a detailed report with findings, risk ratings, and a prioritized roadmap for improvements. Your IT person is probably drowning in break-fix work. Managed IT services complement in-house staff by handling proactive monitoring, strategic projects, and specialized expertise. Think of it as expanding your team’s capacity without hiring overhead. Many businesses find this hybrid model lets their internal IT focus on business-critical projects while we handle the operational load. Test it. Attempt to restore files to a test environment and verify they’re intact and uncorrupted. Do this quarterly. If you’ve never tested your backup, assume it doesn’t work — and then fix it immediately. A backup that’s never been tested is just hope, not a strategy.What’s the most common IT problem Canadian SMBs face?
How much does it cost to fix these problems?
Can we fix these problems ourselves?
How long does an IT assessment take?
What if we already have an IT person on staff?
How do we know if our backup actually works?
Fusion Computing serves Canadian businesses across:
Managed IT — Toronto · Managed IT — Hamilton · Managed IT — Metro Vancouver
Mike Pearlstein is CEO of Fusion Computing and holds the CISSP, the gold standard in cybersecurity certification. He has led Fusion’s managed IT and cybersecurity practice since 2012, serving Canadian businesses across Toronto, Hamilton, and Metro Vancouver.

