PIPEDA Compliance for Canadian Small Businesses: What’s Actually Required in 2026
Written by Mike Pearlstein, CISSP — CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver.
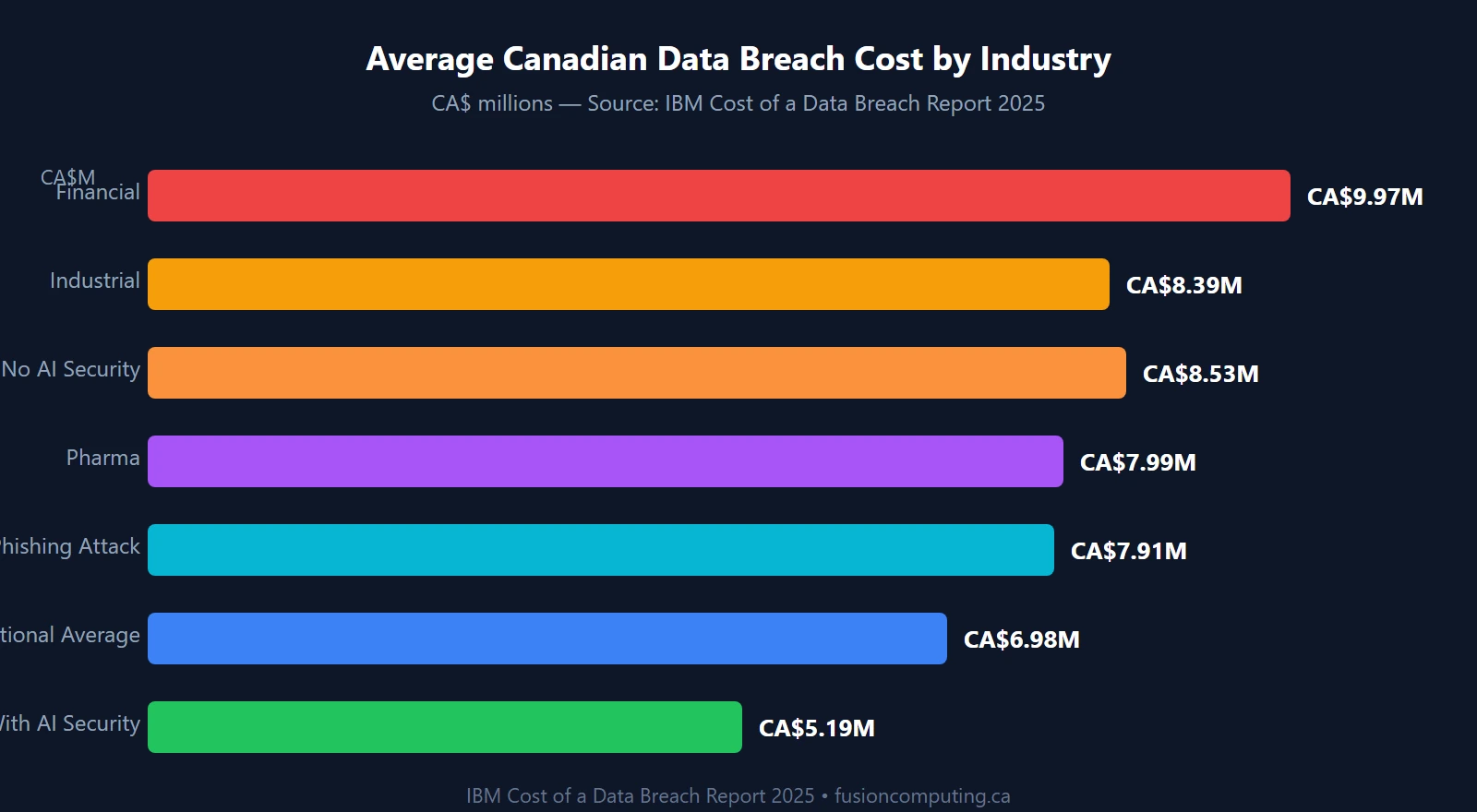
According to IBM’s 2025 Cost of a Data Breach report, the average Canadian data breach now costs CA$6.98 million — up 10.4% from CA$6.32 million in 2024. That number includes regulatory fines, breach response costs, reputational damage, and lost business. What it doesn’t include is the legal exposure that comes from violating Canada’s federal privacy law. PIPEDA — the Personal Information Protection and Electronic Documents Act — has mandatory breach reporting, record-keeping requirements, and penalties up to $100,000 CAD per violation. Most small businesses I meet aren’t ignoring it on purpose. They just don’t know what it actually requires.
This guide fixes that.
Key Takeaways
- PIPEDA applies to virtually every Canadian business engaged in commercial activity — there’s no employee-count exemption.
- The OPC received 686 breach reports from businesses in 2024–25. If your breach poses a “real risk of significant harm,” you’re legally required to report it.
- Bill C-27 (which would have replaced PIPEDA) died in January 2025 when Parliament prorogued. PIPEDA is the law now, with no replacement in sight.
- The Safeguards Principle is the most technically demanding requirement — and the one most SMBs fail. It covers encryption, access controls, employee training, and vendor management.
- Organizations using AI-driven security tools average CA$5.19M per breach vs. CA$8.53M without them (IBM 2025) — a 39% cost difference.
What Is PIPEDA and Does It Apply to Your Business?
PIPEDA is Canada’s federal private-sector privacy law. It governs how organizations collect, use, and disclose personal information in the course of commercial activities. Unlike GDPR, there’s no revenue threshold or employee-count floor — if you run a for-profit business in Canada and handle personal information, PIPEDA almost certainly applies to you.
Personal information under PIPEDA is broad: names, email addresses, IP addresses, purchase history, health information, employee records, and anything else that can identify an individual. That covers pretty much every business with a website, a customer list, or employees.
Who PIPEDA Covers (and the Narrow Exceptions)
PIPEDA applies to private-sector organizations that collect, use, or disclose personal information in the course of commercial activity across Canada or across provincial borders. The law exempts non-commercial activities (a non-profit running a bingo night) and employees of federal works like banks and airlines — but those employees are covered when the same organization handles customer data commercially.
Three provinces — Quebec, British Columbia, and Alberta — have private-sector privacy laws the federal government has deemed “substantially similar.” Businesses in those provinces can rely on provincial law for purely provincial activities. But the moment personal information crosses provincial or international borders — a Toronto supplier sends data to a Vancouver vendor, or you use a US-based CRM — PIPEDA applies to that transaction. In practice, most Canadian SMBs are subject to PIPEDA regardless of where they’re incorporated.
Quebec’s Law 25: Higher Bar Than PIPEDA
If you have Quebec clients or employees, you’re also subject to Quebec’s Act 25 (the modernization of Quebec’s private sector privacy law), fully in force since September 2023. Law 25 is stricter than PIPEDA in several areas: 72-hour breach notification timelines, mandatory privacy impact assessments for high-risk data processing, and a right to data portability. If you’re already compliant with Law 25, you’re largely compliant with PIPEDA federally — but the reverse isn’t necessarily true.
The 10 PIPEDA Fair Information Principles: What They Mean Day-to-Day
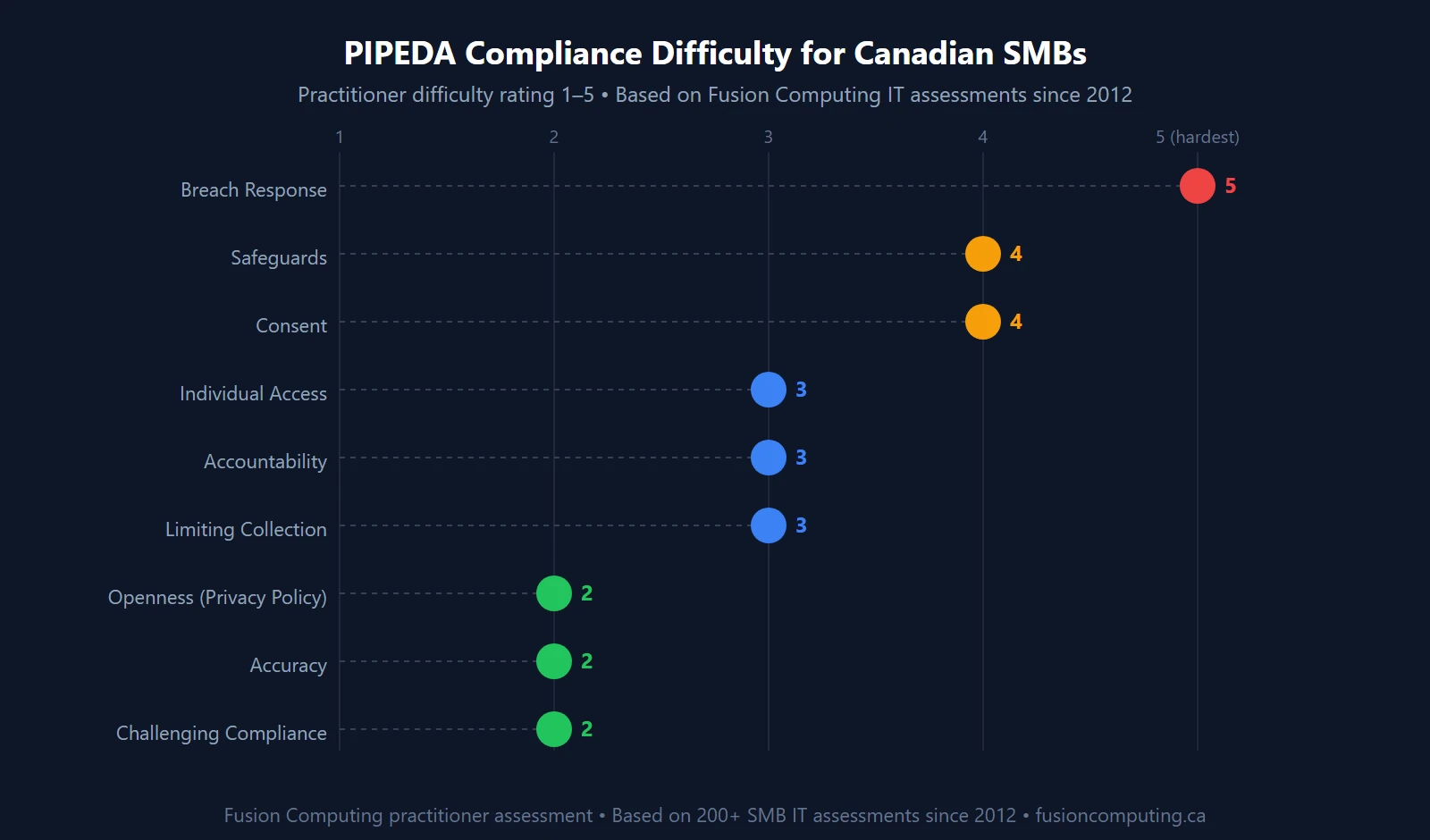
PIPEDA is built around 10 Fair Information Principles set out in Schedule 1. They’re not aspirational guidelines — they’re legally binding obligations. In 12 years running an MSP and doing IT assessments across Toronto, Hamilton, and Metro Vancouver, I’ve seen the same three principles create the most problems for SMBs: Accountability, Safeguards, and Breach Response (which intersects Safeguards and the mandatory reporting regulations added in 2018).
| Principle | Core Obligation | Most Common SMB Gap |
|---|---|---|
| 1. Accountability | Designate someone responsible for PIPEDA compliance | Nobody owns it. “The IT guy” isn’t a privacy officer. |
| 2. Identifying Purposes | State why you’re collecting data before or at time of collection | Contact forms with no stated purpose |
| 3. Consent | Get meaningful consent before collecting personal info | Pre-checked boxes, buried terms, no opt-out for marketing |
| 4. Limiting Collection | Collect only what you need for the stated purpose | Forms asking for birth date, SIN, or income “just in case” |
| 5. Limiting Use & Disclosure | Use data only for the purpose you collected it | Selling or sharing email lists without separate consent |
| 6. Accuracy | Keep personal info accurate for the decisions it informs | No process to update stale client records |
| 7. Safeguards | Protect personal info with appropriate security | No encryption, no MFA, ex-employees with live credentials |
| 8. Openness | Be transparent about your privacy practices | Outdated or copy-pasted privacy policy from a template |
| 9. Individual Access | Let individuals access and correct their personal info | No process to respond to access requests within 30 days |
| 10. Challenging Compliance | Have a complaints process and respond to OPC complaints | No designated contact or documented complaints procedure |
The OPC can now initiate investigations without a complaint, conduct proactive audits of an organization’s privacy practices, and publish findings even where an organization disputes them. That shift — from complaint-driven to proactive — happened quietly but it changed the risk profile for every Canadian business.
Your Mandatory Breach Reporting Obligations Under PIPEDA
Since November 2018, PIPEDA has required organizations to report breaches of security safeguards involving personal information to the OPC and notify affected individuals — but only when the breach poses a “real risk of significant harm.” That phrase does a lot of heavy lifting.
What “Real Risk of Significant Harm” Means
Significant harm under PIPEDA includes bodily harm, humiliation, damage to reputation or relationships, financial loss, identity theft, negative effects on a credit record, and loss of employment or business opportunities. The sensitivity of the information and the probability it’s been misused are the two main factors in making that determination.
A backup drive left in a cab? Probably real risk. A misdirected email with a single client’s name and phone number? Probably not — but you need to document that assessment and keep the record for 24 months. That 24-month record-keeping requirement applies to every breach, whether or not it meets the reporting threshold. Missing records is itself an offence.
The Reporting Timeline
PIPEDA doesn’t specify an exact number of days — it requires reporting “as soon as feasible” after you determine a breach has occurred. In practice, the OPC expects notification within days, not weeks. Compare that to Quebec’s Law 25, which mandates reporting within 72 hours to the Commission d’accès à l’information. If you have Quebec clients, 72 hours is your real deadline.
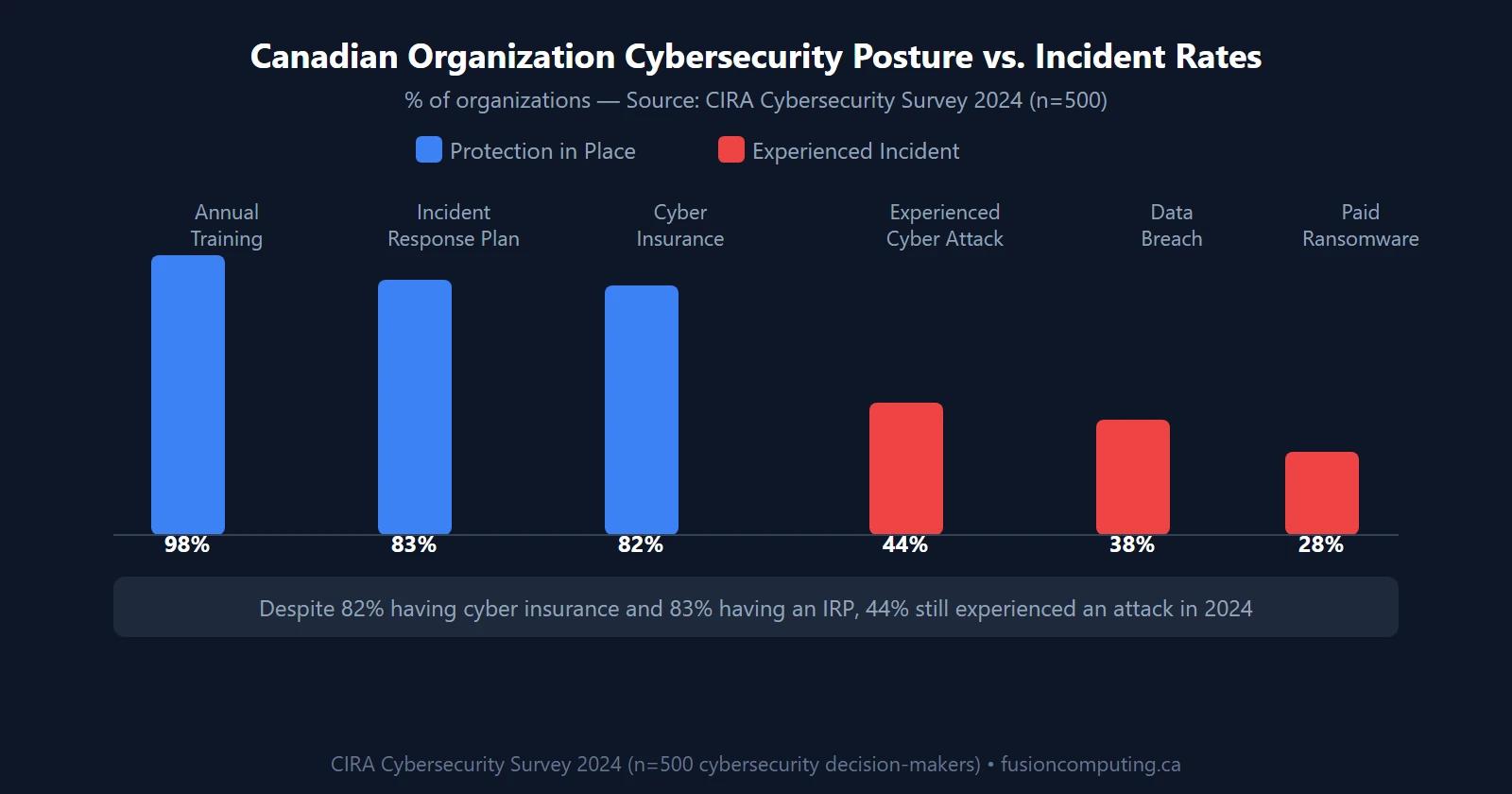
According to the Office of the Privacy Commissioner of Canada’s 2024–25 Annual Report, the OPC received 686 data breach reports from private-sector businesses subject to PIPEDA — and 43% of Canadians surveyed said they’ve already been affected by a privacy breach. Those aren’t edge cases. They’re your clients and your employees.
Penalties for Non-Compliance
Organizations that knowingly fail to report a qualifying breach to the OPC, notify affected individuals, or maintain breach records face fines of up to CA$100,000 per violation. “Per violation” means each affected individual’s failure to notify is potentially a separate violation. If 500 clients were in a breach you failed to report, the math gets ugly fast.
What PIPEDA’s Safeguards Principle Actually Requires from Your IT
The Safeguards Principle is the one that translates directly to your IT environment. PIPEDA requires “appropriate security measures” commensurate with the sensitivity of the data — which sounds vague until you look at OPC guidance. The OPC specifies three categories of safeguards, all of which you need.
Technical Safeguards
Encryption for data at rest and in transit. Access controls limiting who can reach personal information. Multi-factor authentication on accounts that touch client or employee data. Intrusion detection and monitoring. Regular patching to close known vulnerabilities. These aren’t aspirational — they’re explicitly listed in OPC guidance as examples of what “appropriate” looks like.
In our cybersecurity assessments across SMBs in Toronto and Hamilton, the most common Safeguards gaps cluster around three issues: former employees with active credentials, unencrypted backups, and third-party vendor access with no documented agreement. (We find at least one of those three in the majority of initial assessments.)
Organizational Safeguards
Employee training on privacy and data handling. Access controls based on the principle of least privilege — staff see only the data they need for their role. Confidentiality agreements with employees and contractors. A designated privacy officer (even if that’s a named person rather than a dedicated role). These are process controls, not technology — but the OPC expects them.
Fusion Computing’s cybersecurity awareness training covers PIPEDA obligations alongside phishing, password hygiene, and incident response. Training your staff isn’t optional under PIPEDA — it’s part of what “appropriate organizational measures” means.
Physical Safeguards
Locked filing cabinets for physical records. Restricted access to server rooms and network equipment. Clean desk policies for staff who handle sensitive data. Screen locks on unattended workstations. Physical safeguards are low-tech but they’re part of the PIPEDA picture, and the OPC has cited their absence in enforcement decisions.
Is PIPEDA Being Replaced? The Bill C-27 Story and What It Means for 2026
The short answer: no. Not this year, and possibly not for years.
Bill C-27 — the Consumer Privacy Protection Act (CPPA) — would have replaced PIPEDA with a more modern framework closer to GDPR in its approach. It introduced meaningful consent requirements, data portability rights, algorithmic transparency for automated decision-making, and fines up to 5% of global revenue or CA$25 million (whichever is higher). It also bundled Canada’s first federal AI regulation, the Artificial Intelligence and Data Act (AIDA).
In January 2025, Parliament prorogued. Bill C-27 died on the order paper. A federal election in April 2025 pushed privacy reform further into the future. PIPEDA — a law written in 2000 — is still the governing framework for Canadian private-sector privacy, with no replacement timeline confirmed.
What this means for your business: comply with PIPEDA now. Don’t wait for C-27 or a CPPA successor. The enforcement environment under PIPEDA has become more active, not less. And if you build PIPEDA compliance into your IT environment today, you’ll have a head start when stronger legislation eventually arrives — because it will.
Get a Custom IT Assessment for Your Business
The Fusion PIPEDA Readiness Framework: A Self-Assessment for Canadian SMBs
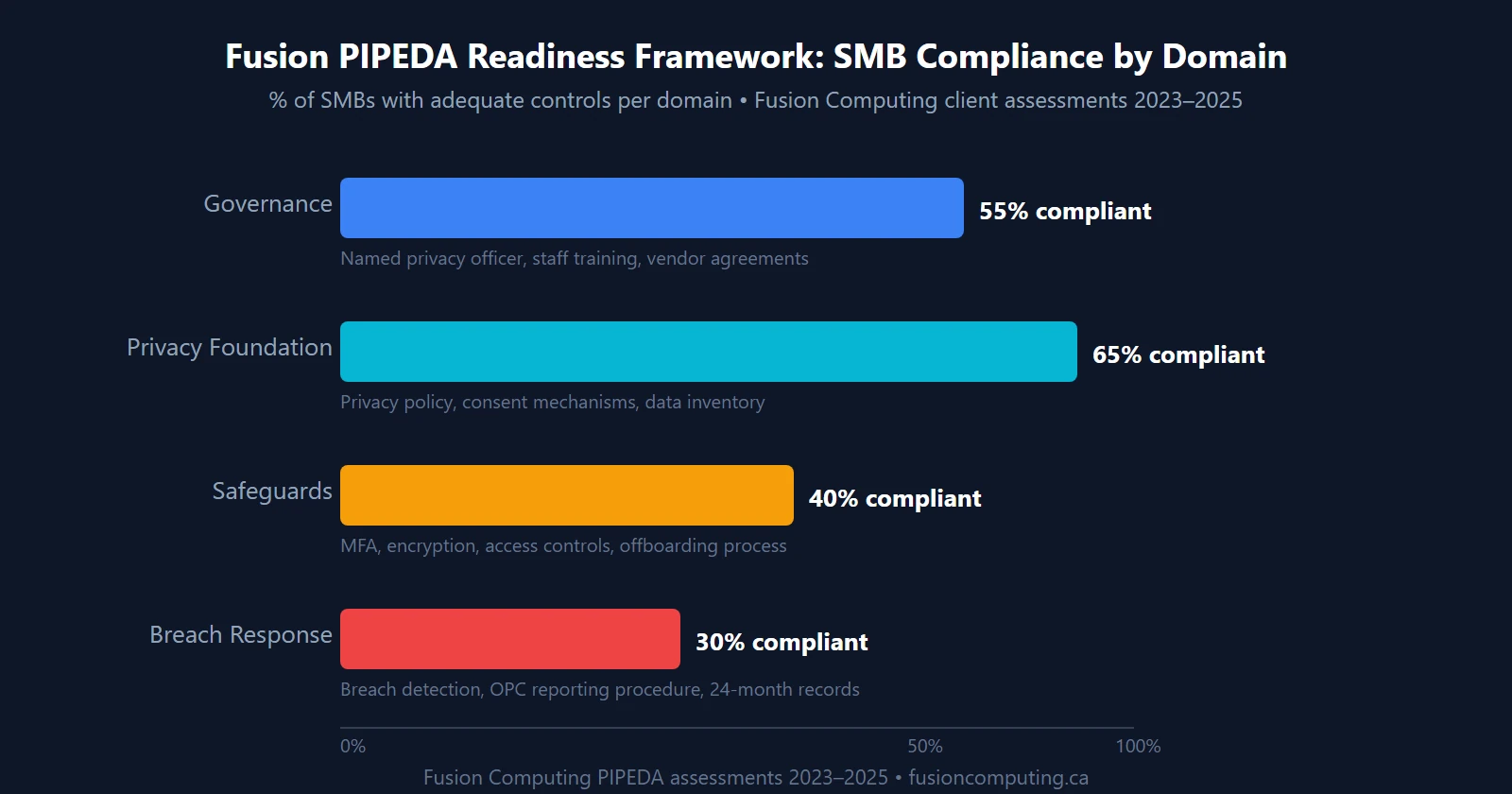
After running IT assessments across hundreds of Canadian SMBs since 2012, we’ve identified four domains where PIPEDA compliance either holds or breaks. We call it the Fusion PIPEDA Readiness Framework — a structured way to audit your current posture before the OPC comes knocking.
| # | Requirement | Domain | In Place? |
|---|---|---|---|
| 1 | Named privacy officer or designated PIPEDA contact | Governance | □ |
| 2 | Published privacy policy that reflects actual data practices | Privacy Foundation | □ |
| 3 | Consent language on all web forms and data collection points | Privacy Foundation | □ |
| 4 | Data inventory: know what personal info you hold and where | Privacy Foundation | □ |
| 5 | MFA enforced on email, CRM, and all accounts touching personal data | Safeguards | □ |
| 6 | Data encryption at rest and in transit (laptops, cloud storage, email) | Safeguards | □ |
| 7 | Offboarding process: credentials revoked within 24h of departure | Safeguards | □ |
| 8 | Vendor data processing agreements for all third parties accessing personal data | Safeguards | □ |
| 9 | Annual privacy and security training for all staff | Governance | □ |
| 10 | Documented breach detection and assessment procedure | Breach Response | □ |
| 11 | OPC breach report template on file and process for completing it | Breach Response | □ |
| 12 | Breach records log maintained (required for 24 months minimum) | Breach Response | □ |
Scoring: 10–12 checks = strong posture. 7–9 = material gaps, prioritize Safeguards and Breach Response first. Below 7 = significant risk exposure. A free IT assessment will identify exactly where your gaps are and what they’ll take to close.

How IT Services Help Canadian Businesses Meet PIPEDA’s Safeguards Principle
The Safeguards Principle is the most technically demanding of the 10 PIPEDA principles. It’s also the one where an MSP adds the most direct value. Here’s what Fusion Computing deploys to help clients meet it:
Cybersecurity services built on the CIS Controls v8.1 framework: endpoint protection, email filtering, vulnerability management, and network monitoring. These aren’t checkbox items — they’re the technical controls the OPC expects to see when investigating a breach. If you can’t demonstrate you had appropriate safeguards in place, you’ll have a harder time arguing the harm wasn’t foreseeable.
Identity and access management covers the offboarding problem and least-privilege access. Every departed employee with active credentials is a PIPEDA liability. Our managed IT services in Toronto and Hamilton include a standard offboarding runbook that revokes credentials across Microsoft 365, line-of-business applications, and VPN within 24 hours of departure.
Virtual CIO services address the governance side — helping you designate a privacy officer, document data flows, draft a privacy policy that reflects what you actually do, and build a breach response plan before you need one. Most SMBs don’t need a full-time privacy counsel. They need a senior advisor who’s done this before and can translate the legal requirements into operational steps.
IT business assessments map your current environment against the Fusion PIPEDA Readiness Framework above. In a typical 168-point assessment, we check encryption posture, access control hygiene, backup integrity, vendor agreement status, and employee training compliance — everything the OPC would look at in a proactive audit.
According to IBM’s 2025 Cost of a Data Breach report, organizations extensively using AI-driven security and automation averaged CA$5.19 million per breach versus CA$8.53 million for those without — a 39% reduction. That gap is large enough to fund a decade of managed IT services. The compliance case and the financial case for proper safeguards are the same case.
If you operate in a regulated sector — law, healthcare, accounting, or financial services — your PIPEDA obligations layer on top of sector-specific requirements. Our cybersecurity services in Toronto and Hamilton include compliance advisory for professional services firms navigating both PIPEDA and their professional body’s cybersecurity standards. The overlap is substantial; the effort to address both together is much lower than treating them separately.
Fusion Computing also helps clients maintain the disaster recovery and incident response capabilities that PIPEDA’s Breach Response domain requires. You can’t document a breach assessment timeline if you don’t have a detection capability. And you can’t notify affected individuals “as soon as feasible” if you don’t know the breach happened.
Fusion Computing helps businesses meet PIPEDA’s Safeguards Principle across
Toronto and the GTA,
Hamilton, and
Metro Vancouver. If you’re not sure where your gaps are, that’s exactly what a free IT assessment is for.
Related Resources
- Data Security & Compliance for Canadian Businesses
- Cyber Insurance Coverage Checklist for Canadian Businesses
- How to Build an Incident Response Plan for Your Small Business
- Cybersecurity Awareness Training for Canadian Small Businesses
- Zero Trust Security for Canadian Small Businesses
- Cybersecurity Assessment Services
- What Are Managed IT Services? A Plain-English Guide
Book a 30-Minute IT Assessment
Frequently Asked Questions About PIPEDA Compliance
What is PIPEDA and does it apply to my small business in Canada?
PIPEDA — the Personal Information Protection and Electronic Documents Act — is Canada’s federal private-sector privacy law. It applies to virtually any for-profit business engaged in commercial activity in Canada that collects, uses, or discloses personal information. There’s no employee-count or revenue threshold. If you have a website contact form, a customer list, or employees, PIPEDA almost certainly applies to you. Businesses in Quebec, BC, and Alberta may rely on substantially similar provincial laws, but PIPEDA still applies when data crosses provincial or international borders.
What are the penalties for violating PIPEDA?
Organizations that knowingly fail to report a qualifying breach to the Office of the Privacy Commissioner of Canada (OPC), fail to notify affected individuals, or fail to maintain breach records for 24 months face fines of up to CA$100,000 per violation. Because “per violation” can apply per affected individual in certain interpretations, the exposure scales quickly with the size of a breach. Non-compliance also triggers OPC investigation authority, which can result in published findings even if no formal fine is levied.
What does PIPEDA require when my business has a data breach?
If a breach of security safeguards poses a “real risk of significant harm” to individuals, you must report it to the OPC and notify affected individuals “as soon as feasible.” Significant harm includes financial loss, identity theft, damage to reputation, and humiliation. You must also maintain records of every breach — whether or not it meets the reporting threshold — for a minimum of 24 months. Failure to keep those records is itself an offence under PIPEDA.
Do I need a privacy policy to comply with PIPEDA?
Yes. PIPEDA’s Openness Principle (Principle 8) requires organizations to be transparent about their information-handling practices and make them readily available. In practice, that means a published privacy policy that accurately describes what data you collect, why you collect it, how you use and protect it, and how individuals can access or correct their records. A template privacy policy copied from a US website probably doesn’t satisfy PIPEDA — it needs to reflect your actual data practices and reference Canadian law.
What IT security measures does PIPEDA require?
PIPEDA’s Safeguards Principle requires “appropriate security measures” proportionate to the sensitivity of the data. The OPC specifies technical safeguards (encryption, access controls, firewalls, intrusion detection), organizational safeguards (staff training, least-privilege access, confidentiality agreements), and physical safeguards (locked cabinets, restricted server access). There’s no single prescribed standard, but organizations using frameworks like CIS Controls v8.1 have a defensible position when demonstrating safeguards to the OPC.
Is PIPEDA being replaced by a new Canadian privacy law?
Not in the near term. Bill C-27 — which would have replaced PIPEDA with the Consumer Privacy Protection Act — died on the order paper in January 2025 when Parliament prorogued. A federal election in April 2025 pushed privacy reform further into the future. PIPEDA remains Canada’s federal private-sector privacy law with no confirmed replacement timeline. Businesses should build PIPEDA compliance into their operations now rather than waiting for a stronger law to force the issue.
How is PIPEDA different from GDPR?
GDPR (Europe’s General Data Protection Regulation) is stricter than PIPEDA in several ways: mandatory 72-hour breach notification, explicit rights to erasure and data portability, higher fines (up to 4% of global revenue or €20 million), and broader territorial scope. PIPEDA doesn’t specify a notification deadline (just “as soon as feasible”), has lower maximum fines, and doesn’t include a formal right to erasure. If you handle EU residents’ data, GDPR may also apply to your business in addition to PIPEDA.
What’s the difference between PIPEDA and Quebec’s Law 25?
Quebec’s Act 25 (fully in force since September 2023) is stricter than PIPEDA in several areas: a mandatory 72-hour breach notification deadline to Quebec’s Commission d’accès à l’information, required privacy impact assessments for high-risk data processing, and a formal right to data portability. If your business has Quebec clients or employees, Law 25 applies — and meeting Law 25’s higher standards means you’re likely compliant with federal PIPEDA as well. For businesses operating only outside Quebec, PIPEDA remains the governing federal framework.

