Cybersecurity Awareness Training for Small Business: A 2026 Canadian Guide
Mike Pearlstein is CEO of Fusion Computing and holds the CISSP, the gold standard in cybersecurity certification. He has led Fusion’s managed IT and cybersecurity practice since 2012, serving Canadian businesses across Toronto, Hamilton, and Metro Vancouver.
KEY TAKEAWAYS
- One-third of untrained employees will click a phishing link. After 12 months of training, that drops to 4.1% – an 86% reduction (KnowBe4, 2025).
- 44% of Canadian organizations experienced a cyber attack in the last 12 months (CIRA, 2024). Human error drives 60% of all breaches globally.
- CIRA offers managed cybersecurity awareness training at $50/user/year for teams under 50 – purpose-built for Canadian small businesses.
- Most cyber insurance policies now require documented security awareness training to qualify for coverage.
- PIPEDA doesn’t mandate training by name, but the Privacy Commissioner’s guidance treats it as a necessary safeguard – and fines reach $100,000 per violation.
Cybersecurity awareness training teaches your employees to recognize and avoid the attacks that technical controls can’t stop. Phishing emails, social engineering calls, credential theft – these aren’t software problems. They’re people problems. And they account for 60% of all data breaches, according to the Verizon 2025 Data Breach Investigations Report.
The good news? Training works. Not the annual compliance slideshow that everyone clicks through in January. Real training – monthly modules, simulated phishing, measurable behaviour change. KnowBe4’s 2025 benchmark data across 14.5 million users shows that phishing click rates drop from 33.1% to 4.1% after 12 months of consistent training. That’s an 86% reduction in your single biggest attack surface.
This guide covers what a cybersecurity awareness training program should include for a Canadian small business, what it costs, how to implement one, and how to measure whether it’s actually working.
Book a Free Cybersecurity Assessment
Why does cybersecurity awareness training matter for small businesses?
Security awareness training matters because your employees are the primary target, not your firewall. Attackers don’t brute-force their way through enterprise-grade security. They send a well-crafted email to an accounts payable clerk at 4:45 p.m. on a Friday. And it works – far more often than most business owners realize.
The Verizon 2025 DBIR found that phishing was the top tactic in 57% of social engineering incidents, with 60% of all breaches involving a human element. That’s not a technology gap. That’s a training gap.
Canadian small businesses are hit disproportionately hard. Statistics Canada reported that 16% of Canadian businesses experienced a cybersecurity incident in 2023. But here’s the number that should worry you: according to a BDC poll from September 2024, 61% of Canadian business owners still believe larger companies are more likely to be hacked. They’re wrong. Small businesses don’t make headlines, but they make easy targets.
Fusion Computing deploys security awareness training as part of every managed cybersecurity engagement. Across our Canadian client base, we’ve seen baseline phishing click rates of 25–35% drop to under 5% within six months of launching monthly training and phishing simulations. The pattern is consistent: the first simulation is humbling, but month-over-month improvement is almost immediate.

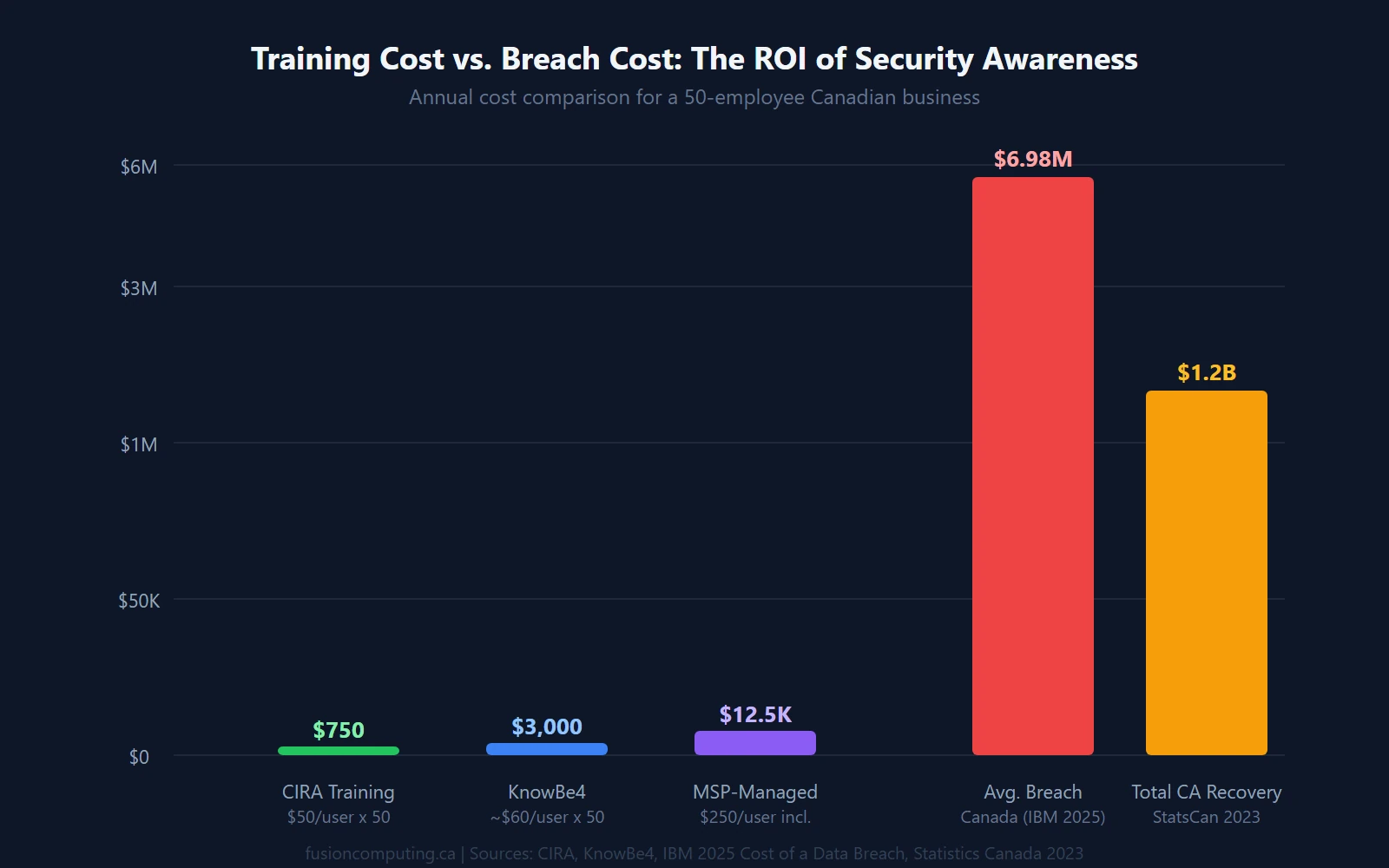
How much does cybersecurity awareness training cost in Canada?
Cybersecurity awareness training costs between $15 and $60 per user per year for a Canadian small business, depending on the platform, team size, and whether phishing simulations are included. That’s $1.25 to $5.00 per user per month – less than a single coffee per employee.
For context, the IBM 2025 Cost of a Data Breach Report puts the average breach cost at US$4.44 million globally, with human error responsible for 26% of those breaches. You don’t need a calculator to see the ROI.
Here’s what the Canadian market looks like in 2026:
| Platform | Annual Cost/User | Best For | Phishing Sims | Canadian Content |
|---|---|---|---|---|
| CIRA | $50 CAD | Teams ≤ 50 users | Yes (monthly) | Yes – Canadian-built |
| KnowBe4 | US$18–$30 | 25–500+ users | Yes (extensive library) | Limited |
| Proofpoint (Wombat) | US$25–$50 | 50–1,000+ users | Yes | No |
| ESET | US$20–$35 | 10–250 users | Yes | Partial |
| MSP-bundled | Included in managed IT | All sizes | Varies | Depends on MSP |
For Canadian businesses under 50 employees, CIRA’s small teams program is the strongest value. At $50 CAD per user per year, you get a fully managed training pipeline with monthly phishing simulations, courseware, user dashboards, and a gamified risk scoring system. It’s built by the same organization that manages .ca domain registrations – they understand the Canadian threat landscape.
What matters more than the platform is whether you actually use it. We’ve seen $30/user platforms outperform $50/user platforms because the cheaper one was deployed with monthly cadence and management buy-in, while the expensive one sat in a procurement spreadsheet.
What should a cybersecurity awareness training program cover?
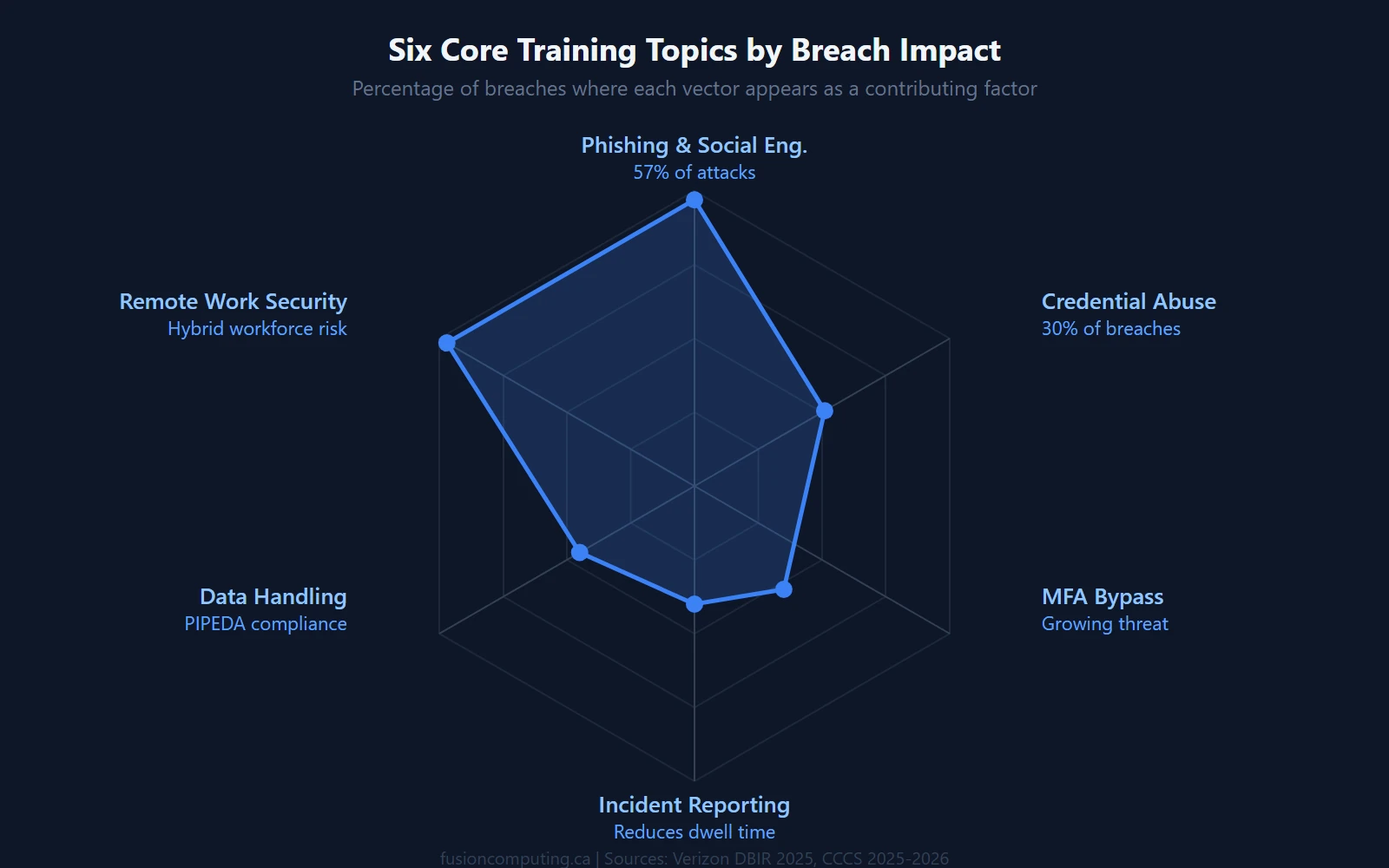
An effective security awareness training program covers six core threat categories, each tied to real attack patterns that the Canadian Centre for Cyber Security identifies as active threats against Canadian organizations.
Here’s what your training should include – and why each topic earns its place:
1. Phishing and social engineering recognition
This is the foundation of any phishing awareness training program. Staff need to identify suspicious sender addresses, urgency triggers, impersonation attempts, and URL manipulation. The Canadian Centre for Cyber Security recommends tailoring scenarios to your industry – a construction company’s phishing templates should look different from an accounting firm’s.
2. Password hygiene and credential security
Credential abuse appears in 30% of breaches involving human error (Verizon 2025 DBIR). Train staff on password managers, the death of password rotation as a policy, and why reusing credentials across personal and work accounts is a direct threat to your business. For a deeper dive, see our guide to password security for business.
3. Multi-factor authentication
MFA blocks 99.9% of credential-based attacks, according to Microsoft. But it only works if employees understand how to use it, why it matters, and what MFA fatigue attacks look like. Cover push-notification bombing, SIM swapping, and the shift to phishing-resistant FIDO2 keys. See our breakdown of multi-factor authentication for business.
4. Safe browsing and remote work security
With hybrid work now the default for most Canadian businesses, employees need to understand public Wi-Fi risks, VPN usage, and the difference between personal and corporate device policies. This connects directly to remote work cybersecurity best practices.
5. Data handling and PIPEDA compliance
Your staff handle personal information daily – client records, HR data, financial details. Under PIPEDA, your organization is responsible for protecting it. Training should cover what constitutes personal information, proper handling procedures, and what to do if they suspect a breach. For more on compliance obligations, see our data security and compliance guide.
6. Incident reporting procedures
The fastest way to contain a breach is to catch it early. Employees need a clear, non-punitive reporting path: who to call, what to document, and what not to touch. This dovetails with your incident response plan – if you don’t have one, build it before launching your training program.
How do you implement a cybersecurity training program? The 5-Phase Framework
Implementing cybersecurity awareness training takes 4–6 weeks from platform selection to first phishing simulation, and the process follows five phases. We’ve deployed this framework across dozens of Fusion Computing clients, from 8-person design studios to 200-employee manufacturing operations.
Phase 1: Baseline assessment (Week 1)
Before you train anyone, measure where you stand. Run an unannounced phishing simulation to establish your baseline click rate. Don’t warn staff. Don’t send a company-wide email about “upcoming security testing.” You need a clean number.
KnowBe4’s 2025 data puts the global baseline at 33.1%. In our Canadian client base, we typically see 25–35% on the first simulation. That’s one in three employees handing over credentials or clicking a malicious link.
This phase also includes a cybersecurity assessment to identify technical gaps that training alone can’t fix. If your email gateway isn’t filtering properly, training is fighting uphill.
Phase 2: Platform selection and configuration (Week 2)
Choose a platform based on your team size, budget, and compliance requirements. For most Canadian businesses under 50 employees, CIRA is the right starting point. Over 50, you’re looking at KnowBe4, Proofpoint, or an MSP-managed solution.
Configuration includes importing your user list, setting up phishing simulation templates, selecting courseware modules, and establishing your training cadence. Monthly is the minimum. Quarterly isn’t enough – CIRA’s own research found that employees who received weekly phishing simulations were 2.74 times more effective at reducing phishing risk than those trained quarterly.
Phase 3: Launch training and first module (Week 3)
Start with a foundational module – the “what and why” of cybersecurity for your team. Keep it under 15 minutes. Include a quiz. Then follow immediately with your first announced phishing simulation so staff can apply what they just learned.
Getting leadership buy-in here is critical. When the CEO completes the training first and talks about it, participation rates jump. When it’s treated as an “IT thing,” completion rates plateau at 60–70%.
Phase 4: Monthly cadence and reinforcement (Weeks 4–12)
This is where the real behaviour change happens. The monthly rhythm should look like:
- Week 1: Short training module (5–10 minutes) on a specific topic
- Week 2: Unannounced phishing simulation
- Week 3: Results review and targeted follow-up for clickers
- Week 4: Quick reinforcement (poster, Slack message, or micro-lesson)
The KnowBe4 2025 benchmark shows a 40% reduction in click rates after just 90 days of this cadence, and 86% after 12 months.
Phase 5: Measure, report, and iterate (Quarterly)
Every quarter, review your metrics against your baseline. Report results to leadership – not just click rates, but reporting rates (how many employees flagged the simulation), completion rates, and trend direction. Adjust your simulation difficulty upward as your team improves.
This is also where cyber insurance documentation matters. Your insurer wants evidence of ongoing training, not a one-time checkbox. Quarterly reports give you exactly that.
Get a Cybersecurity Assessment for Your Team
How effective is security awareness training? The data behind the investment
Security awareness training reduces phishing susceptibility by 86% over 12 months, according to KnowBe4’s 2025 analysis of 14.5 million users across 62,400 organizations and 67.7 million simulated phishing tests. That’s the largest dataset ever published on training effectiveness.

Here’s the timeline:
- Baseline: 33.1% of untrained employees click simulated phishing links
- After 90 days: Click rate drops by 40% – roughly 1 in 5 instead of 1 in 3
- After 12 months: Click rate reaches 4.1% – that’s 86% lower than baseline
The most at-risk industries? Healthcare and pharmaceuticals at 41.9%, insurance at 39.2%, and retail at 36.5%. If your business falls into one of those categories, you’re starting from a higher baseline and the training ROI is even stronger.
On the Canadian side, the 2024 CIRA Cybersecurity Survey found that 44% of Canadian organizations experienced a cyber attack in the preceding 12 months, and 98% now conduct some form of cybersecurity awareness training. But “some form” is doing a lot of heavy lifting in that statistic – there’s a world of difference between an annual PDF and a monthly simulation program.
We saw this firsthand with a client who came to us after a ransomware incident. Their previous “training” had been a single onboarding email. Within three months of implementing monthly simulations, their click rate went from 32% to 8%.
What are the PIPEDA and cyber insurance implications?
PIPEDA doesn’t explicitly mandate cybersecurity awareness training, but the Privacy Commissioner’s guidance treats it as a necessary safeguard – and failing to train your staff can expose you to fines of up to $100,000 per violation.
Here’s the regulatory landscape Canadian businesses need to understand:
PIPEDA safeguard requirements
The Office of the Privacy Commissioner has issued guidance specifying that safeguards should include “organizational measures such as training, access controls, and confidentiality agreements.” While the legislation doesn’t spell out “thou shalt train thy employees,” the OPC has been clear: if a breach occurs and you can’t demonstrate that your staff were trained on data handling, your safeguards will be found inadequate.
Organizations that knowingly fail to report a breach, notify affected individuals, or maintain breach records face fines of up to $100,000 CAD per violation. Training documentation is your evidence that reasonable safeguards were in place.
Cyber insurance training requirements
This one’s simpler: most cyber insurance policies in 2026 require documented security awareness training as a condition of coverage. It sits alongside MFA, endpoint detection, and incident response plans as a core underwriting requirement.
According to multiple insurer analyses, the standard requirements now include:
- MFA for email, remote access, and administrative accounts
- A documented employee security awareness training program with phishing simulations
- Endpoint detection and response (not just traditional antivirus)
- A written, tested incident response plan
- Immutable backups with tested disaster recovery procedures
If you can’t demonstrate training, you may not qualify for coverage – or you’ll pay significantly higher premiums. And if a claim arises and your insurer discovers you lapsed on training, they can deny the claim entirely. Our cyber insurance checklist covers the full list of requirements.
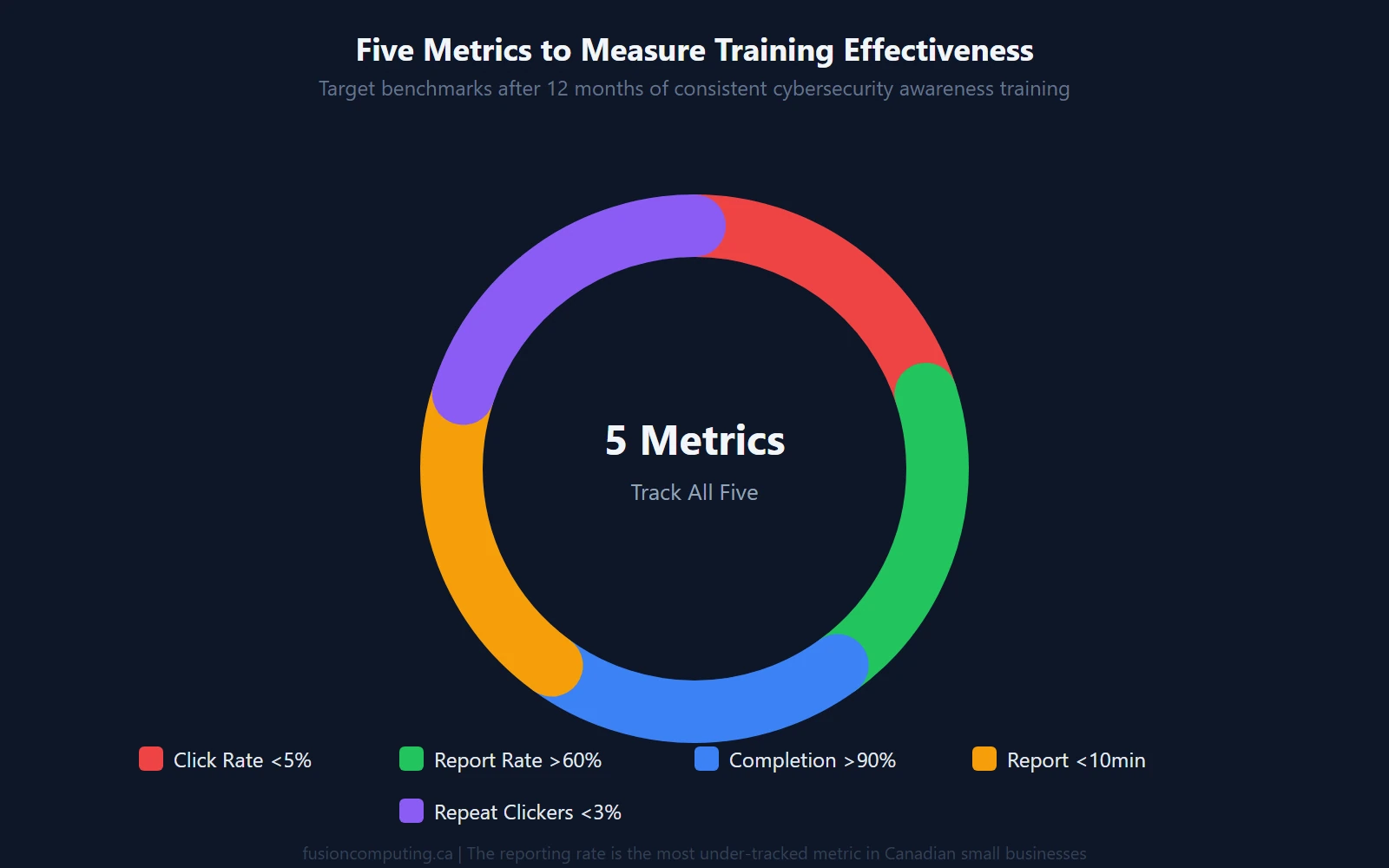
How do you measure cybersecurity training effectiveness?
Measure training effectiveness with five metrics: phishing click rate, reporting rate, completion rate, time-to-report, and repeat clicker rate. Tracking just one – the click rate – misses the bigger picture.
| Metric | What It Measures | Target (12-month) | Why It Matters |
|---|---|---|---|
| Phishing click rate | % who click simulated phishing links | < 5% | Direct measure of susceptibility |
| Reporting rate | % who flag suspicious emails | > 60% | Shows active vigilance, not just avoidance |
| Completion rate | % who complete monthly modules | > 90% | Program engagement and leadership support |
| Time-to-report | Minutes from phishing receipt to report | < 10 min | Speed determines containment success |
| Repeat clicker rate | % who click > 1 simulation | < 3% | Identifies who needs additional intervention |
The reporting rate is the one most organizations ignore – and it’s arguably more important than the click rate. A team that clicks 5% of phishing emails but reports 70% of them is in much better shape than a team with a 3% click rate and a 10% reporting rate. The first team catches threats. The second one just gets lucky.
Cybersecurity awareness training self-assessment checklist
Use this checklist to evaluate where your organization stands today. Score yourself honestly – each “No” represents a gap that attackers can exploit.
| # | Control | Category | In Place? |
|---|---|---|---|
| 1 | Monthly cybersecurity training modules for all employees | Program | □ |
| 2 | Simulated phishing campaigns at least monthly | Testing | □ |
| 3 | Baseline phishing click rate measured | Measurement | □ |
| 4 | Phishing reporting button in email client | Infrastructure | □ |
| 5 | Leadership completes training alongside staff | Culture | □ |
| 6 | Targeted remediation for repeat clickers | Program | □ |
| 7 | Training records maintained for cyber insurance/compliance | Documentation | □ |
| 8 | Non-punitive reporting culture (no blame for honest mistakes) | Culture | □ |
| 9 | New hire security orientation within first week | Onboarding | □ |
| 10 | Quarterly metrics review reported to management | Measurement | □ |
Scoring: 8–10 checks = Strong. 5–7 = Functional gaps that increase risk. Under 5 = Your organization is operating without a meaningful security culture. A cybersecurity assessment can help you prioritize what to fix first.
Looking for cybersecurity awareness training in your region?
Fusion Computing delivers managed cybersecurity services – including security awareness training, phishing simulations, and ongoing monitoring – to businesses across three Canadian markets:
- Cybersecurity Services in Toronto & the GTA – serving Toronto, Mississauga, Brampton, Markham, Vaughan, Richmond Hill, and surrounding areas
- Cybersecurity Services in Hamilton – serving Hamilton, Burlington, Dundas, Ancaster, Stoney Creek, and the Niagara Region
- Cybersecurity Services in Metro Vancouver – serving Vancouver, Burnaby, Richmond, Surrey, Coquitlam, and North Vancouver
Book Your Free IT Business Assessment
Related resources
- Cybersecurity Services for Canadian Businesses
- Cybersecurity Assessment
- Incident Response Plan for Small Business Canada
- Cyber Insurance Coverage Checklist
- Benefits of Multi-Factor Authentication for Business
- Are Your Passwords Secure? A Business Guide
- Why Cybersecurity Is Important for Canadian Businesses
- Zero Trust Security for Canadian SMBs
Frequently asked questions about cybersecurity awareness training
How often should employees receive cybersecurity awareness training?
Monthly training with simulated phishing campaigns is the minimum effective cadence. CIRA’s research shows that employees who receive weekly phishing simulations are 2.74 times more effective at reducing risk than those trained quarterly. Annual compliance training alone doesn’t change behaviour – it checks a box.
How much does cybersecurity awareness training cost for a small business in Canada?
Between $15 and $60 per user per year, depending on the platform and team size. CIRA’s Canadian program costs $50 CAD per user per year for teams under 50 employees and includes monthly phishing simulations. MSP-managed programs often bundle training into their monthly per-user fee at no extra charge.
Is cybersecurity training required by Canadian law?
PIPEDA doesn’t mandate training by name, but the Privacy Commissioner’s guidance includes employee training as a necessary safeguard for protecting personal information. Organizations that fail to maintain adequate safeguards – including training – face fines of up to $100,000 CAD per violation under PIPEDA’s breach notification rules.
Does cyber insurance require employee cybersecurity training?
Yes. Most cyber insurance policies in 2026 require a documented security awareness training program with phishing simulations as a condition of coverage. Insurers also require multi-factor authentication, endpoint detection and response, and a tested incident response plan. Without training documentation, you risk claim denial or higher premiums.
What’s the biggest mistake companies make with security awareness training?
Treating it as a one-time event instead of an ongoing program. A single annual training session doesn’t change behaviour – it creates a false sense of compliance. The organizations that see real results run monthly modules, track click rates and reporting rates over time, and treat repeat clickers with additional coaching rather than punishment.
How do I measure whether cybersecurity training is working?
Track five metrics: phishing click rate (target under 5%), reporting rate (target over 60%), module completion rate (target over 90%), time-to-report (target under 10 minutes), and repeat clicker rate (target under 3%). The reporting rate is the most important and the most under-tracked – it measures whether employees are actively identifying threats, not just avoiding them.
What topics should cybersecurity training cover?
Six core areas: phishing and social engineering recognition, password hygiene and credential security, multi-factor authentication usage, safe browsing and remote work practices, data handling and PIPEDA compliance, and incident reporting procedures. The Canadian Centre for Cyber Security recommends tailoring scenarios to your specific industry and business operations.

