According to IBM’s 2025 Cost of a Data Breach report, the average cyber incident costs Canadian businesses CA$6.98 million (Mordor Intelligence)–a figure that’ll spell financial ruin for small operations or serious disruption for larger ones. Cyber insurance has become essential, with over 59% of Canadian businesses now carrying some form of coverage. The Canadian cyber insurance market was valued at USD $0.59B in 2025 and is projected to reach $1.14B by 2030 at a 14.24% CAGR. But here’s the question most businesses don’t ask until it’s too late: does your policy actually pay out when you need it? This guide walks you through the complete checklist for qualifying in 2026.
If you’re using this checklist to close underwriting gaps, the next practical step is our cybersecurity services page for managed controls and monitoring, plus our IT assessment page if you want a concrete remediation plan from a Canadian team.
KEY TAKEAWAYS
- Cyber insurance premiums are climbing because carriers now require documented security controls before they’ll underwrite.
- MFA, EDR, backup verification, and an incident response plan are the minimum requirements for most cyber insurance policies in 2026.
- Your policy may not cover what you think it covers. Review exclusions for social engineering, supply chain attacks, and nation-state actors.
TL;DR
Cyber insurers now require MFA, EDR, encrypted backups, and an incident response plan before approving coverage. 40% of claims are denied for failing these controls. Your checklist should verify breach notification costs, ransomware recovery, business interruption, and regulatory fines are covered. Fusion Computing helps Canadian businesses pass insurer security assessments and maintain continuous compliance.
What does cyber insurance actually cover?
Cyber insurance is a liability policy that covers financial losses from cybersecurity incidents including data breaches, ransomware attacks, business interruption, regulatory fines, and notification costs. In Canada, cyber insurance isn’t legally mandatory for most businesses but is increasingly required by enterprise clients, contracts, and industry regulations as a condition of doing business.
Cyber insurance isn’t legally mandatory for most Canadian businesses, but it’s increasingly required by clients, contracts, and industry regulations. Many enterprise customers now require their vendors to carry cyber liability coverage. Insurers also require specific security controls. MFA, EDR, backups, incident response plans. before they’ll underwrite a policy, making it a de facto compliance driver.
A cyber insurance coverage checklist should verify: breach response and notification costs, ransomware payment and recovery, business interruption and lost revenue, regulatory fines and penalties, third-party liability, forensic investigation costs, credit monitoring for affected individuals, and legal defense expenses. Most insurers require MFA, endpoint protection, backup verification, and employee training as minimum security controls.
TL;DR
Cyber insurance covers financial losses from data breaches, ransomware, business interruption, regulatory fines, and liability claims. Most policies require baseline security controls (MFA, EDR, backups, patching) as preconditions for coverage. Canadian businesses should review their cyber insurance annually to ensure coverage limits match their risk profile and that security requirements align with their actual controls.
Cyber insurance is a policy that protects businesses against financial losses from cyberattacks, including breach investigation costs, ransomware payments, legal fees, regulatory fines, customer notification expenses, and business interruption losses. In 2026, Canadian insurers require documented security controls – MFA, EDR, tested backups, and an incident response plan – before they’ll underwrite a policy.
Cyber insurance protects your business against losses from successful attacks. This includes financial losses from the breach itself, ransom or extortion costs, forensic investigation and remediation expenses, regulatory fines and penalties, legal fees, customer notification costs, crisis management and PR expenses, business interruption losses, and third-party liability claims. The specifics vary by policy, but understanding what’s covered helps you build a meaningful checklist for your business.
Fusion Computing is a CISSP-certified managed security services provider (MSSP) serving Canadian businesses since 2012. All security operations align to CIS Controls v8.1, with 24/7 managed detection and response, endpoint protection, and incident response. Delivered from Canadian offices with all data stored in Canada.
The 2026 Qualification Checklist: What Insurers Now Require
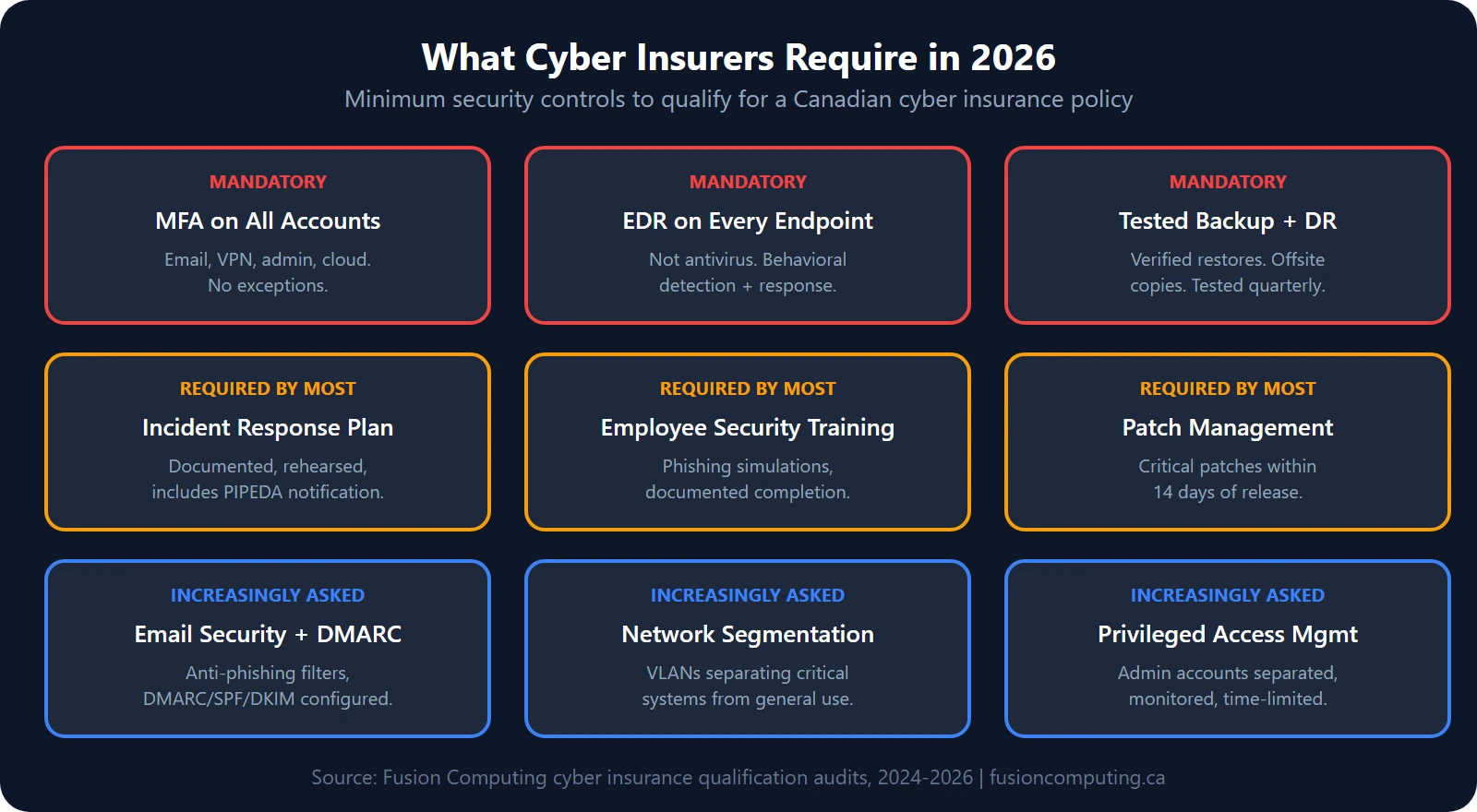
Canadian cyber insurance carriers have tightened their underwriting standards significantly. Whereas five years ago insurers would issue policies with minimal questions, 2026 carriers now demand documented security controls before issuing a quote. Here’s the core checklist that separates approved applicants from denied claims.
1. Multi-Factor Authentication (MFA) Across All User Accounts
MFA is now non-negotiable. Carriers require MFA enabled on all user accounts, particularly email, administrative access, and financial systems. This single control prevents approximately 90% of credential-based attacks. Most insurers won’t quote a policy without evidence that MFA is enforced organization-wide. Acceptable implementations include hardware tokens, authenticator apps, or push-based mobile authentication.
2. Endpoint Detection and Response (EDR) or Equivalent Monitoring
EDR solutions provide continuous visibility into what’s happening on every workstation and server. Carriers expect you to deploy EDR tools that monitor file execution, memory injection, and lateral movement attempts. That’s how you demonstrate you can detect an attack in progress rather than discovering it weeks later. Many 2026 policies explicitly name EDR as required; others accept equivalent monitoring solutions like SIEM or XDR platforms.
3. Automated Backup and Disaster Recovery Systems
Backup systems must be immutable and kept offline or in an isolated location that ransomware can’t reach. Carriers scrutinize your recovery time objective (RTO) and recovery point objective (RPO). The requirement is typically: daily backups, tested recovery at least twice per year, and documented proof of successful restores. Backups stored on the same network as production systems don’t meet modern insurance requirements.
4. Documented Incident Response Plan
You must have a written, tested incident response plan that names roles, responsibilities, and escalation procedures. The plan should cover breach notification timelines, forensic vendor contacts, executive communication protocols, and regulatory reporting. Carriers now request evidence of a tabletop exercise or simulated incident within the past 12 months. A plan that’s never been tested doesn’t carry much weight.
5. Mandatory Cybersecurity Training for All Staff
Annual security awareness training is now standard. Carriers expect proof of phishing simulation campaigns, with documented results showing click rates and employee participation. Training should cover password hygiene, phishing recognition, social engineering tactics, and incident reporting procedures. Some insurers require quarterly training rather than annual; check your underwriter’s specific mandate.
6. Annual Vulnerability Scanning and Penetration Testing
Automated vulnerability scanning must run on all internet-facing assets at least quarterly. Annual penetration testing by a third party–either full-scope or targeted to high-risk systems–is now expected. Carriers want documentation of discovered vulnerabilities and remediation timelines. A policy without evidence of regular security testing will face premium penalties or outright denial.
7. Patch Management and System Updates
Documented patching schedules are required. Most carriers expect security patches deployed within 30 days of release; critical patches within 7–14 days. You must maintain a log or registry showing patch deployment dates across all systems. Unpatched systems or evidence of delayed patches will mean premium increases or coverage exclusions.
8. Data Inventory and Classification
You must maintain a complete inventory of where sensitive data is stored, who accesses it, and how it’s protected. This includes customer records, employee information, financial data, and intellectual property. Carriers want to see evidence that you understand your data footprint and have classified it by sensitivity level. Vague answers or admissions that you’re unsure where data lives are major red flags.
Get a Custom IT Assessment for Your Business
First-Party vs. Third-Party Coverage: Understanding the Split
Cyber policies split into two coverage buckets. First-party coverage pays your expenses: forensic investigation, data recovery, customer notification, credit monitoring, and business interruption losses. Third-party coverage handles claims from customers, business partners, or regulators harmed by your breach. Most small businesses won’t think about first-party limits, but if you process customer data or operate in regulated industries, third-party limits are equally critical. Ensure your policy clearly defines both limits.
Book a Cybersecurity Assessment
Why do cyber insurance claims get denied?
Insurers deny cyber claims far more often than most business owners realize. According to industry data, over 40% of businesses that file cyber insurance claims receive no payout, and 82% of denials involve organizations without MFA. The most common denials result from: failure to maintain required security controls (MFA, backups, EDR); voluntary fund transfers due to social engineering or executive override; breach discovery after policy expiration; poor housekeeping on patch schedules; and prior knowledge of a vulnerability that was not disclosed at underwriting. A second common trigger is miscommunication at policy application: if you claim MFA is enabled but it’s not, your claim can be denied as fraudulent misrepresentation.
How a Managed IT Services Provider (MSP) Helps You Qualify and Stay Compliant
Qualification’s only half the battle; staying compliant throughout the year is just as demanding. An MSP serves as your implementation and monitoring partner. A good MSP will: design and deploy the security controls your insurer requires; maintain documented evidence of compliance (logs, reports, test results); perform monthly security reviews to catch gaps before your insurer does; conduct the required annual penetration testing; support employee training and phishing simulations; and maintain your incident response plan and disaster recovery procedures. When a claim occurs, the MSP provides forensic documentation and timeline evidence that supports your position with the carrier.
How do you apply for cyber insurance in Canada?
When applying for cyber insurance in 2026, assume that your insurer (IntelTech notes insurers want proof, not promises: screenshots, logs, backup test results, security reports)’ll verify every claim you make. Answer the underwriting questionnaire with complete honesty. If you claim MFA is enforced but 20% of users lack it, you’ve created grounds for a denial. If you say you’ve got a documented incident response plan, be ready to provide it. Insurers increasingly hire third-party assessors to conduct pre-quote security assessments; some policies now require a formal audit before issuance. This extra scrutiny is frustrating, but it’s because claim disputes over missing controls have become costly and common.
What’s changing in the cyber insurance market in 2026?
The cyber insurance market is evolving rapidly. S&P Global Ratings reports that global cyber insurance premiums grew 7% in 2025 to $15.3B, with a forecast 15–20% increase in 2026. Carriers are tightening underwriting, raising premiums, and excluding entire industries or company sizes that they view as too risky. Ransomware sub-limits are becoming standard (often capping ransom coverage at 10–20% of total policy limits). Some insurers are now offering premium discounts (typically 10–15%) for businesses that implement CIS Controls v8.1 or adopt a zero trust security model, frameworks that align closely with what carriers want to see. Third-party liability exclusions are expanding; some carriers are now excluding certain types of third-party claims altogether. If you’re shopping for a new policy or renewing an existing one, ask your broker specifically what has changed since last year.
How do you get started: Your Action Plan?
Begin by conducting a gap analysis: compare your current security controls against the checklist above. Identify which controls are in place, which need improvement, and which are missing entirely. Engage an MSP or security consultant to help fill gaps and document compliance. Allow 60–90 days for control implementation before applying for new coverage or renewing existing policies. Once controls are in place, work with your broker to find carriers that match your risk profile and budget. Don’t settle for a policy that doesn’t require the controls you’ve worked hard to implement; that means you’ve invested in security that your insurer doesn’t value.
Cyber Liability Insurance in Canada: What SMBs Need to Know
Cyber liability insurance covers the financial fallout from data breaches, ransomware attacks, and privacy violations. Including legal defence costs, regulatory fines, customer notification expenses, and business interruption losses. For Canadian businesses, policies typically range from CA$1,500–$10,000/year for $1M–$5M in coverage, depending on revenue, industry, and security posture.
What most Canadian SMBs don’t realize until renewal:
- Premiums are tied to your security controls. Businesses with EDR, MFA, and an incident response plan pay significantly less than those without
- Carriers audit at renewal. The questionnaire you filled out at purchase becomes a compliance checklist. If your controls have lapsed, your claim can be denied.
- PIPEDA breach notification is mandatory. Since 2018, Canadian businesses must report breaches that pose a “real risk of significant harm.” Your cyber insurance should cover the notification costs.
There’s a direct connection between managed cybersecurity and cyber liability insurance is direct: the controls your MSP deploys are the same controls your insurer requires. That’s not a coincidence. It’s the business case for managed security.
Internal Links to Key Resources
To strengthen your qualifying position, consider these Fusion Computing services:
- Cybersecurity Services — thorough security program design and deployment
- Cybersecurity Assessment — formal audit of your current state
- Incident Response Plan for Small Business — develop a tested response playbook
- IT Support Toronto. Managed IT and monitoring for GTA businesses
- IT Support — ongoing monitoring and patch management
- Managed IT Services — full stack control and compliance management
- Security and Vulnerability Assessment — annual scanning and penetration testing
- Multi-Factor Authentication — MFA design and deployment
- IT Business Assessment — understand your current risk posture
- Contact Us for a consultation
Cyber Insurance Coverage Checklist: Reviewing Your Policy Before Renewal
Walking through a cyber insurance coverage checklist before every renewal protects your organization from gaps that accumulate as your business grows. Coverage that’d fit your risk profile two years ago may leave critical exposures uncovered today. Insurance coverage evolves alongside underwriting standards, and insurers are regularly adding new exclusions or sub-limits that change what your policy actually pays.
What Your Insurance Coverage Should Include in 2026
A solid coverage checklist for a Canadian SMB should confirm first-party loss coverage (breach response, business interruption, ransom), third-party liability limits, regulatory defense costs, and social engineering fraud. Review each category annually against your current revenue, data volume, and business operations. Many organizations discover their policy limits were set based on outdated business size — a risk that only surfaces during a claim.
Matching Coverage to Your Organization’s Risk Profile
Every organization carries a different risk profile. A professional services firm handling regulated client data faces different exposure than a manufacturer with industrial control systems. Your cyber insurance coverage checklist should reflect your specific threat landscape. Work with a broker who’s familiar with your industry. A generic policy won’t cover the exact incident type your business is most likely to face.
Get Insurance-Ready: Book an Assessment
Fusion Computing helps businesses qualify for cyber insurance across Toronto & GTA | Hamilton | Metro Vancouver
Why Fusion Computing is Your Partner in Cyber Insurance Readiness
At Fusion Computing, we’ve guided over 200 Canadian businesses through cyber insurance qualification since 2012. We understand what carriers expect because we work directly with underwriters and brokers. Our CISSP-certified leadership brings real-world experience in designing compliant security programs. We excel at first-contact resolution: when you engage us, we deliver a gap assessment, implementation roadmap, and ongoing compliance monitoring in a single integrated engagement. We’re familiar with the requirements of major Canadian insurers and can advise on which carriers align best with your business profile and budget.
According to Fortune Business Insights, the global cyber insurance market reached $26.25B in 2025, with projections to $223.47B by 2034 at 27% CAGR—underscoring why qualification requirements aren’t getting easier any time soon.
External References and Citations
For current cyber insurance trends and regulatory guidance, consult:
- Insurance Bureau of Canada — statistics on cyber claims and market trends
- Canadian Centre for Cyber Security — CCCS guidance on baseline security controls and incident reporting
Not sure if your business would pass a cyber insurance application today? Fusion Computing can run a gap analysis and help you qualify.
Book a Cybersecurity Assessment
Related Resources
Concerned About Your Cybersecurity Posture?
Find out where your organization stands with a free cybersecurity assessment from our CISSP-certified team.
Cyber Insurance Control Requirements
| Control | Required by Most Insurers | Premium Discount Trigger |
|---|---|---|
| Multi-factor authentication | Yes. All remote access | 5–15% discount |
| EDR/MDR on all endpoints | Yes. Since 2024 | 5–10% discount |
| Offline/immutable backups | Yes. Tested quarterly | 5–10% discount |
| Employee security training | Yes. Annual minimum | 3–5% discount |
| Incident response plan | Yes. Documented + tested | 5–8% discount |
| Privileged access management | Increasingly required | 3–5% discount |
Book a 30-Minute IT Assessment
What happens if I apply for cyber insurance without MFA enabled?
Most carriers will either decline to quote or will require MFA deployment as a condition of coverage. Some insurers’ll quote a policy with an exclusion stating they won’t cover losses from compromised credentials. That effectively leaves you uninsured for the most common attack vector. Implementing MFA isn’t optional in 2026.
Can I get cyber insurance if I don’t have a formal incident response plan?
You can apply, but you’ll face higher premiums, lower coverage limits, or outright denial. Carriers view an untested response plan as a signal that you’ll struggle during an actual incident, leading to higher claims costs. A documented plan that has been tested through tabletop exercise shows discipline and reduces carrier risk.
How often should I update my cyber insurance policy to stay current with 2026 requirements?
Review your policy annually at minimum, and anytime your business changes significantly: new data types, expanded operations, industry regulation changes, or after a security incident. Insurance requirements evolve quickly; a policy that qualified last year may have new mandatory controls this year. Schedule a policy review with your broker at least 60 days before renewal.
What is the difference between EDR and traditional antivirus, and why do insurers prefer EDR?
Traditional antivirus relies on signature matching and is reactive—it catches known malware after it’s detected. EDR monitors behavior in real time, detects unknown or zero-day attacks, and provides forensic data about how an attack progressed. Carriers prefer EDR because it gives you a fighting chance to detect and stop an attack mid-course rather than discovering it weeks later.
If I have cyber insurance, do I still need to maintain strong cybersecurity practices?
Absolutely. Insurance covers losses after an attack; strong security prevents the attack from happening in the first place. Carriers require you to maintain reasonable controls as a condition of coverage. Lax security can result in a denied claim or non-renewal. Think of cyber insurance as a safety net, not a substitute for a solid security program.
How much does it cost to implement the controls required for cyber insurance qualification?
Costs vary based on company size and current maturity. A small business (10–50 people) with basic controls in place might invest $15,000–$30,000 to reach full 2026 compliance. A mid-market company (100–500 people) typically invests $50,000–$150,000. The investment usually pays for itself through insurance premium reductions within 2–3 years, plus the reduction in actual breach risk.
Fusion Computing serves Canadian businesses across:
Cybersecurity Services. Toronto · Cybersecurity Services. Hamilton · Cybersecurity Services. Vancouver
About the Author: Mike Pearlstein is CEO of Fusion Computing and holds the CISSP, the gold standard in cybersecurity certification. He’s led Fusion’s managed IT and cybersecurity practice since 2012, serving Canadian businesses across Toronto, Hamilton, and Metro Vancouver.

