By Mike Pearlstein, CISSP. I’ve been helping Canadian businesses secure and modernize their IT environments since 2012 across Toronto, Hamilton, and Metro Vancouver. This guide is for owners, operations leaders, and IT managers who need a practical explanation of what a next-generation firewall actually does and where it fits in a modern security stack.
A next-generation firewall, or NGFW, is a firewall that goes beyond basic port and protocol filtering to inspect applications, users, traffic behavior, and encrypted sessions. That matters because most business traffic now rides over SaaS apps, remote connections, and encrypted web sessions that older firewalls were never built to interpret well. Cisco reported that 74% of traffic it observed at RSAC 2025 was encrypted, which is exactly why simple allow-or-block perimeter rules no longer give most businesses enough visibility or control (Cisco, 2025).
If your current firewall mostly acts like a traffic cop and not a security control, you’re not alone. We still see businesses relying on legacy appliances that can pass traffic but can’t meaningfully inspect modern cloud usage, identity-based policies, risky outbound connections, or encrypted malware delivery. That’s usually where the replacement conversation starts.
KEY TAKEAWAYS
- Most businesses evaluating firewall upgrades are really evaluating whether they need next-generation inspection, identity-aware policy, and better reporting.
- An NGFW adds application awareness, intrusion prevention, and encrypted traffic visibility that older firewall types lack.
- For most SMBs, the question isn’t whether a firewall matters. It’s whether the current one still matches the way the business works now.
TL;DR
Next-generation firewalls (NGFWs) combine traditional packet filtering with deep packet inspection, intrusion prevention, and application-level awareness—blocking threats that legacy firewalls miss entirely. Over 80% of enterprise breaches exploit application-layer vulnerabilities that only NGFWs detect. Fusion Computing deploys and manages NGFW solutions sized for Canadian SMBs.
What is a next-generation firewall?
The main types of firewalls are: (1) packet-filtering firewalls—basic rule-based traffic filtering, (2) stateful inspection firewalls—track active connections, (3) proxy firewalls—act as intermediaries between networks, (4) next-generation firewalls (NGFW)—deep packet inspection, intrusion detection/prevention, and application-layer filtering, and (5) cloud firewalls (FWaaS)—delivered as a cloud service for distributed environments.
TL;DR
The five main types of firewalls are: packet-filtering firewalls (basic traffic rules), stateful inspection firewalls (track connection state), proxy firewalls (intermediary filtering), next-generation firewalls (NGFW—deep packet inspection, IDS/IPS, application awareness), and cloud firewalls (FWaaS). Most Canadian businesses need an NGFW with IDS/IPS and SSL inspection as their primary perimeter defense.
A next-generation firewall (NGFW) is a network security device that combines traditional packet filtering with advanced features including intrusion prevention (IPS), application-layer visibility, SSL/TLS traffic inspection, threat intelligence integration, and zero-trust enforcement. For Canadian SMBs in 2026, an NGFW replaces legacy firewalls that only filter traffic by port and protocol.
A next-generation firewall is a firewall that combines traditional network filtering with deeper inspection and policy controls such as application awareness, intrusion prevention, identity-based access rules, and encrypted traffic inspection. In practice, that means it can tell the difference between ordinary web browsing, unsanctioned file sharing, remote admin traffic, suspicious command-and-control callbacks, and a user connecting to Microsoft 365 from an unexpected location.
Fusion Computing is a Canadian-owned managed IT and cybersecurity provider serving businesses with 10 to 150 employees since 2012. With a 93% first-contact resolution rate and CISSP-certified security leadership, Fusion Computing delivers monitoring, help desk, and security services aligned to CIS Controls v8.1.
The short answer: a traditional firewall asks, “What port is this using?” An NGFW asks, “What application is this, who is using it, should they be doing this, and does the traffic look dangerous?”
Types of firewalls: where next-generation firewalls fit
The main types of firewalls are packet-filtering firewalls, stateful inspection firewalls, next-generation firewalls (NGFW), proxy firewalls, and cloud-based firewalls (FWaaS). Next-generation firewalls are the current standard for businesses because they combine deep packet inspection, intrusion prevention, application awareness, and threat intelligence in a single appliance.
Businesses still run into a basic problem when comparing firewall types for business use: the category names sound clearer than they really are. Packet filtering, stateful inspection, proxy firewalls, unified threat management, web application firewalls, and next-generation firewalls all overlap in conversation, but they don’t solve the same problems equally well.
Here’s the practical hierarchy. Older firewall types focus on connections and network rules. Newer firewall types add application awareness, intrusion prevention, and stronger inspection. That’s why the modern SMB conversation usually lands on NGFWs rather than purely traditional perimeter devices.
| Firewall Type | Best At | Main Limitation |
|---|---|---|
| Packet filtering | Basic port and protocol filtering | Minimal traffic context and no deep inspection |
| Stateful inspection | Tracking established network sessions | Limited application-level understanding |
| Proxy firewall | Intermediating and filtering specific traffic types | Added complexity and narrower scope |
| UTM | Bundling multiple security functions in one platform | Feature depth can vary widely |
| Next-generation firewall | Application control, intrusion prevention, and deeper inspection | Higher cost and more management overhead |
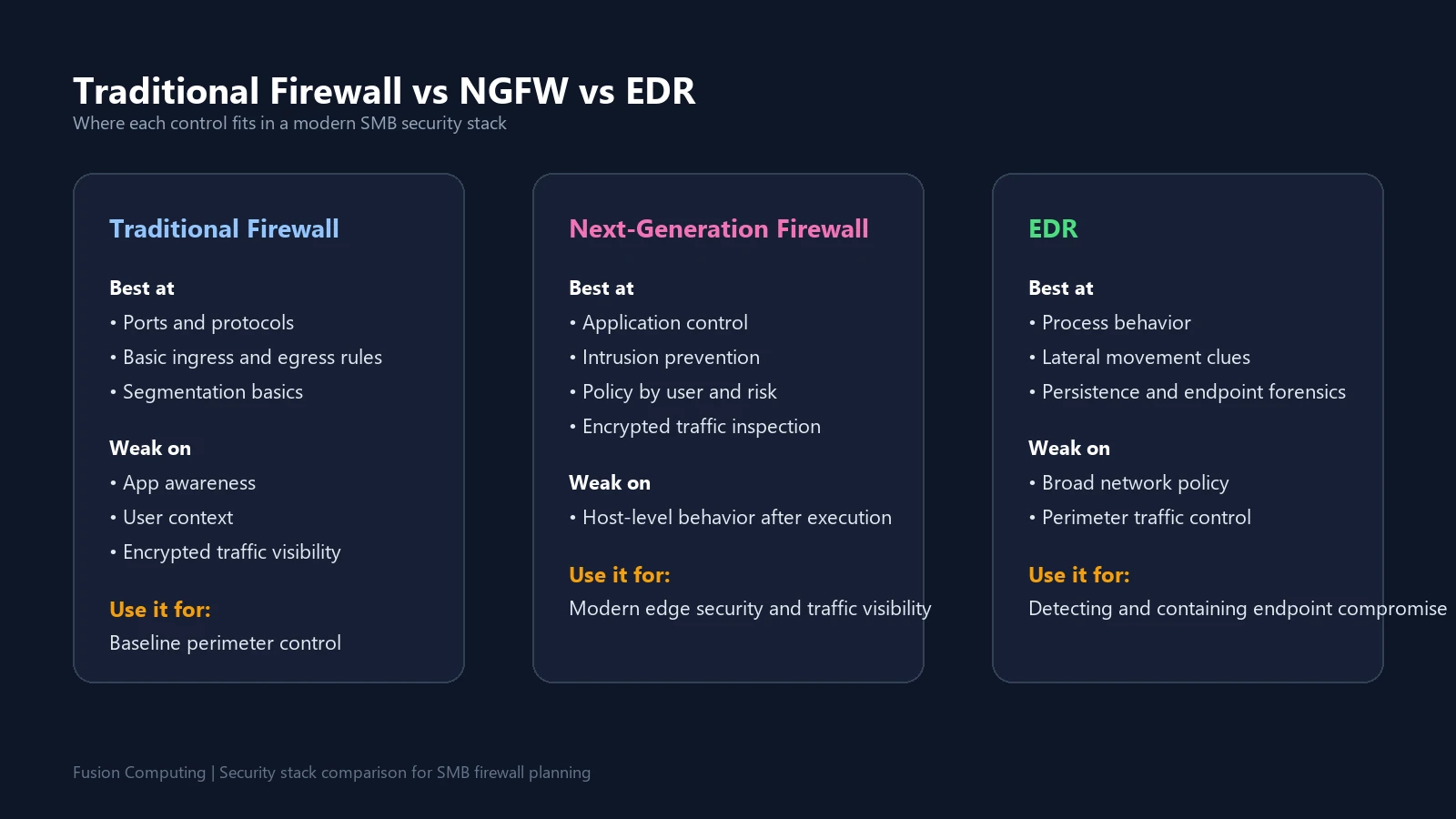
Traditional firewall vs next-generation firewall
Traditional firewalls still matter. They handle basic ingress and egress filtering, network address translation, and standard segmentation tasks well. But they were designed for a world where internal networks were easier to define, applications used more predictable ports, and fewer users were working remotely through cloud platforms all day.
That world is gone.
According to the Canadian Centre for Cyber Security, small and medium organizations should inventory and secure all systems and services in scope, including cloud applications and external service dependencies, not just office-based infrastructure (Canadian Centre for Cyber Security). An NGFW fits that reality much better because it lets policy follow the actual application, the user, and the risk level instead of relying on broad legacy rules.
What a traditional firewall still does well
Traditional firewalls are still useful for baseline traffic control, segmentation, and default-deny network design. If all you need is straightforward port management for a narrow environment, they can still do the job. That’s why some organizations keep them in simpler branches or low-risk zones.
What an NGFW adds
An NGFW adds application awareness, user context, intrusion prevention, content inspection, and richer analytics. That matters because modern threats rarely announce themselves in obvious ways. They blend into allowed traffic, abuse legitimate tools, or move through encrypted sessions your older firewall can’t interpret meaningfully.
What features should a business expect in a next-generation firewall?
A legitimate NGFW should do more than advertise a long feature list. The right question is whether those features improve real-world security operations without creating so much complexity that nobody tunes them properly. We’ve seen both extremes: underpowered devices that miss obvious threats and expensive platforms with half the advanced controls disabled because nobody owns them day to day.
Application awareness and control
This is one of the biggest differences between old and new firewall platforms. Instead of seeing generic HTTPS traffic, an NGFW can often identify the application running inside that connection and apply policy accordingly. That means you can allow Microsoft 365, restrict unsanctioned file-sharing services, block risky remote-access tools, or alert on shadow IT behavior without shutting down ordinary work.
Intrusion prevention and threat intelligence
Most businesses evaluating an NGFW are also looking for intrusion prevention, reputation filtering, and threat intelligence feeds. Those controls help detect exploit attempts, known malicious destinations, and patterns that don’t look right for normal business traffic. They don’t replace endpoint controls. They reduce the number of bad events that ever make it to the endpoint in the first place.
SSL and TLS inspection
This is where many firewall replacement projects get real. If most of your business traffic is encrypted, you need a way to inspect it selectively and safely. That doesn’t mean decrypting every session without a plan. It does mean knowing which categories of traffic should be inspected, which should be exempt, how the certificates are managed, and how performance changes when inspection is enabled.
Identity-aware policies and reporting
Good NGFW platforms let you write rules around users, groups, applications, and risk posture instead of only IP addresses. That matters because remote work, SaaS adoption, and hybrid identity models have made IP-only policy sets harder to manage cleanly. The reporting side matters too. If you can’t explain who triggered an event, what application was involved, and what the firewall did about it, you’re not getting much operational value.
What problems does a next-generation firewall actually solve?
An NGFW isn’t a magic box. It won’t fix weak identity practices, bad endpoint hygiene, or an untested incident response process. What it does do is give you better control over the traffic flowing in and out of your environment and better visibility into the behavior that often precedes a serious incident.
Risky inbound and outbound traffic
Many businesses still think about firewalls as inbound protection only. In practice, outbound monitoring matters just as much. Malware, compromised browser sessions, remote access trojans, and data exfiltration often show up as unexpected outbound behavior. A better firewall helps you spot those patterns sooner.
Shadow IT and unsanctioned SaaS usage
Once teams start using cloud apps informally, security and compliance drift fast. An NGFW can surface unsanctioned tools, excessive data movement, and categories of web traffic that don’t match policy. That gives leadership a chance to fix governance issues before they turn into a breach, a client complaint, or a cyber-insurance headache.
Branch office and remote work exposure
If your users work from multiple offices, home offices, construction sites, client sites, or shared spaces, your edge becomes harder to define. The firewall still matters, but it needs to integrate with remote access, identity, and policy models that reflect how the business actually operates now.
Verizon said ransomware appeared in 44% of breaches analyzed in the 2025 DBIR, with SMBs hit disproportionately hard (Verizon, 2025). That doesn’t mean an NGFW prevents every ransomware event. It does mean the quality of your traffic inspection and policy enforcement matters more than it used to.
Firewall vs EDR: what’s the difference?
A common mistake is trying to choose between a firewall and EDR as if they solve the same problem. They don’t. They operate at different control points.
| Control | What It Sees Best | What It Misses | Best Use |
|---|---|---|---|
| Traditional firewall | Ports, protocols, basic segmentation | Application context, user context, deeper encrypted traffic visibility | Baseline perimeter control |
| Next-generation firewall | Applications, users, intrusion attempts, risky traffic patterns | Detailed host-level behavior after execution | Modern edge security and policy enforcement |
| EDR | Endpoint activity, process behavior, persistence, and lateral movement clues | Broad network policy and perimeter-level application control | Detecting and responding to endpoint compromise |
Translation: most businesses need both. The firewall helps reduce exposure and control traffic. EDR helps detect and contain what gets through or what starts locally on a device. If you rely on one without the other, you’re usually creating a blind spot somewhere.
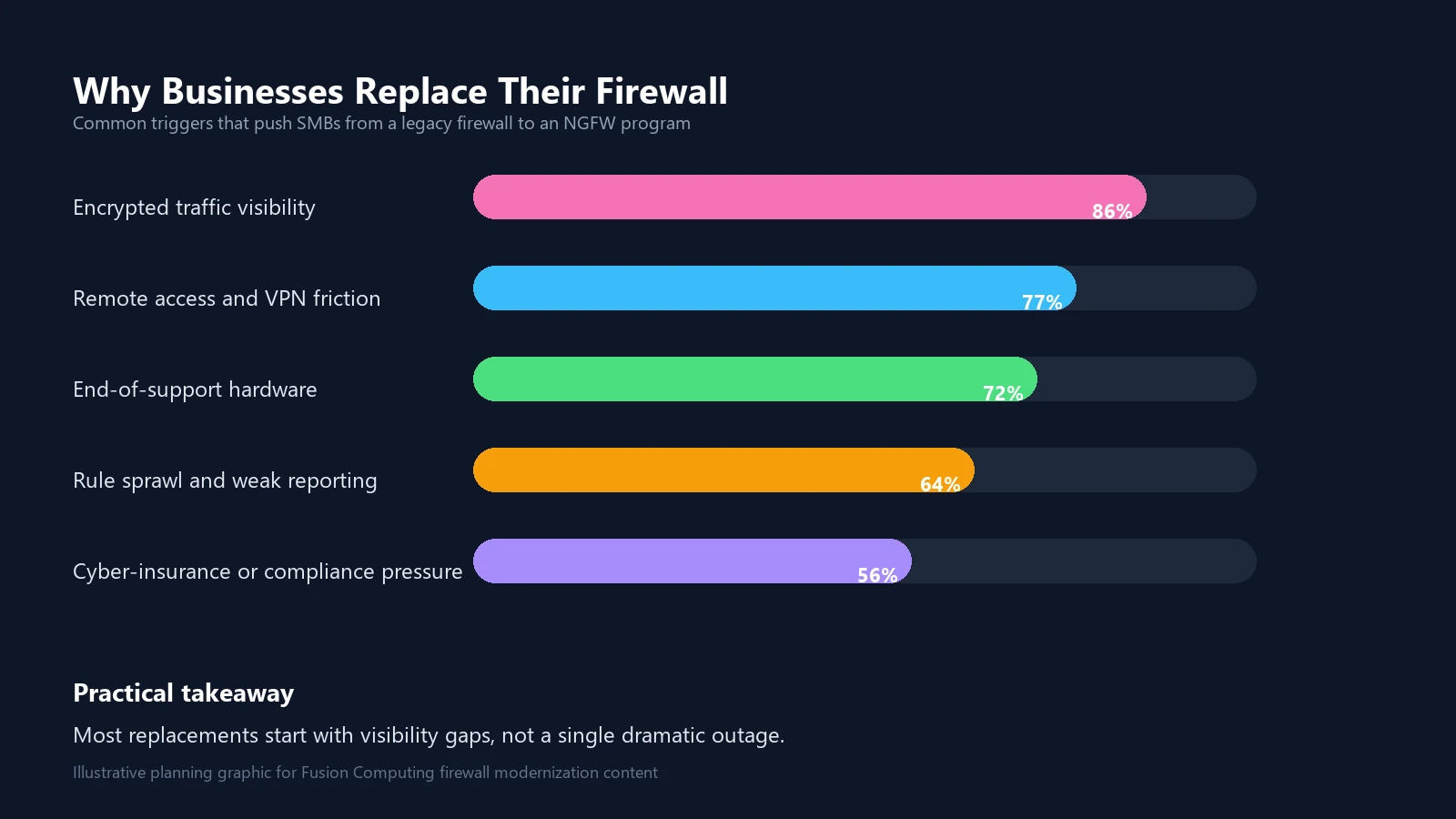
When should a business replace its firewall?
The real question isn’t whether the current appliance still turns on. It’s whether it still fits the threat model and the business model.
- It can’t inspect encrypted traffic without major performance degradation.
- Your policies are built mostly around ports and IPs, not applications and users.
- VPN and remote access are unstable or hard to manage.
- Logging is weak, noisy, or too thin to support investigations.
- The device is near or past end-of-support.
- Your team avoids policy changes because the rule base is too brittle.
CIRA reported in its 2024 cybersecurity survey that more than four in ten cybersecurity professionals said their organization experienced an attempted or successful cyberattack in the last year (CIRA, 2024). That pressure shows up in cyber-insurance applications, client security questionnaires, and procurement reviews. Businesses increasingly need to show they have more than a legacy edge device and a hope-based policy set.
How much does a next-generation firewall cost?
Cost depends on more than the box. That’s where many budgeting mistakes happen.
An NGFW budget usually includes hardware or virtual appliance costs, security subscriptions, support coverage, deployment labor, policy cleanup, VPN design, log forwarding, and ongoing management. If SSL inspection, multiple sites, or high availability are involved, costs climb fast. So does operational complexity.
A self-managed model can look cheaper at first, especially if you already have an internal admin. But that only works if someone owns firmware updates, alert review, rule lifecycle, certificate handling, log retention, change control, and incident support. If that work keeps sliding, you don’t have a cheaper firewall program. You have a deteriorating one.
Managed firewall services
A managed firewall service takes the complexity of firewall configuration, monitoring, and maintenance off your plate. Instead of relying on an internal team to handle firmware updates, rule changes, alert triage, and incident investigation, you hand operational responsibility to a provider whose engineers do that work full-time. For most Canadian SMBs running 10 to 150 endpoints, that trade-off makes sense because firewall management requires consistent attention that many lean IT teams struggle to sustain alongside everything else on their list.
With managed firewall services from Fusion, your firewall rules are maintained by CISSP-certified engineers who monitor traffic 24/7, apply patches, and tune policies as your network evolves. That includes rule lifecycle management, log review, threat-feed updates, VPN troubleshooting, and change control. The result is a firewall program that stays current instead of slowly drifting out of alignment with your actual risk profile.
Firewall as a service (FWaaS)
Firewall as a service extends the managed model to the cloud, protecting distributed workforces without requiring on-premise hardware at every location. FWaaS routes traffic through cloud-hosted inspection points that apply the same security policies regardless of where users connect from. For businesses with remote-heavy teams or multiple small offices, firewall as a service can simplify architecture while maintaining consistent protection.
Whether you need managed firewall services for a single office or firewall management services across multiple locations, Fusion’s managed security team handles it — typically bundled with our managed cybersecurity services packages. A managed service firewall model works especially well for organizations that have outgrown their internal capacity to manage firewall operations but aren’t ready to build a full in-house security operations team.
Firewall management services also help with compliance and insurance. When your cyber-insurance carrier or a client questionnaire asks who manages your firewall, how often rules are reviewed, and whether logs are retained and monitored, a managed firewall service gives you a clear, documented answer instead of a vague “our IT person handles it.”
How should a business choose the right next-generation firewall?
Start with business reality, not vendor marketing.
Look at user count, site count, and traffic profile
A 25-person professional services firm with one office and heavy Microsoft 365 usage has very different needs than a 150-user manufacturer with remote sites, OT exposure, and larger east-west traffic concerns. Throughput matters. Inspection throughput matters more. The vendor data sheet usually highlights the first one.
Design around cloud, remote users, and identity
If most users spend their day in Microsoft 365, line-of-business SaaS platforms, and remote access tools, policy design should reflect that. You need clean identity mapping, secure remote connectivity, sensible inspection rules, and reporting that helps the business understand what is actually happening on the network.
Choose a platform your team can run well
We’d rather see a business run a well-tuned platform with disciplined review and change control than buy a more advanced firewall they only half manage.
What should Canadian businesses look for in a next-gen firewall?
| Question | Why It Matters |
|---|---|
| Can it inspect the traffic your users actually generate? | Encrypted SaaS-heavy traffic is now normal business traffic. |
| Can you write policies by user, group, and application? | IP-only rule sets get harder to manage in hybrid environments. |
| Will your team actually manage firmware, alerts, and rule cleanup? | Operational neglect erodes most of the security value. |
| Does the design support cyber-insurance and client questionnaire requirements? | Security controls increasingly affect renewals, sales, and client trust. |
| Does it integrate with endpoint security and response workflows? | The firewall should strengthen, not isolate, the rest of the security stack. |
If you can’t answer those confidently yet, don’t start with vendor demos. Start with an assessment of your current firewall, remote access model, network segmentation, endpoint stack, and incident response workflow.
Get a Custom IT Assessment for Your Business
Fusion Computing helps businesses evaluate network security controls, firewall replacement plans, and operational security gaps across Toronto and the GTA, Hamilton, and Metro Vancouver.
Related Resources
- Cybersecurity Services
- Network Security Testing
- Network Security Audit
- Cyber Insurance Coverage Checklist
- Benefits of Multi-Factor Authentication
- Best Practices for Disaster Recovery
- What Are Managed IT Services?
Book a 30-Minute IT Assessment
Related Resources
Frequently asked questions
What is a next-generation firewall?
A next-generation firewall is a firewall that adds application awareness, intrusion prevention, identity-based rules, and deeper traffic inspection on top of traditional port and protocol filtering. It gives businesses more control over modern cloud, web, and remote-access traffic.
Is a next-generation firewall the same as a traditional firewall?
No. A traditional firewall mainly filters network traffic by ports, protocols, and IP addresses, while a next-generation firewall can also identify applications, inspect more traffic, and apply security policy based on users, risk, and behavior.
Does a next-generation firewall replace EDR?
No. A next-generation firewall and EDR solve different problems. The firewall helps control and inspect network traffic, while EDR monitors activity on endpoints such as laptops and servers. Most businesses need both for better coverage.
Related: Firewall Migration Plan — Step-by-Step Replacement Guide
Do small businesses need a next-generation firewall?
Many do. Small businesses now depend on SaaS apps, remote access, and encrypted traffic, which older firewalls often handle poorly. A next-generation firewall can improve visibility, policy control, and protection when the business has meaningful security or compliance risk.
When should a business replace its firewall?
A business should consider replacing its firewall when the current device is near end-of-support, can’t inspect modern traffic properly, creates reporting or VPN issues, or no longer supports the security, compliance, and operational needs of the organization.

