IT Support & Cybersecurity for Construction Companies
Multi-site connectivity, mobile device management, and cybersecurity for Canadian construction firms.
Fusion provides managed IT support and cybersecurity for construction companies managing projects across multiple sites. CISSP-certified leadership, CIS Controls alignment, and support for Procore, Sage 300, and field devices.
Best fit for construction firms with 10 to 150 employees.
IT Support & Cybersecurity for Construction Companies
Construction firms manage complex projects across multiple job sites, with field crews, subcontractors, and office staff all depending on systems that need to work reliably. Project management platforms, estimating software, accounting systems, mobile devices, and shared drives are the backbone of daily operations — and when any of them go down, projects stall, deadlines slip, and money is lost. Fusion Computing provides managed IT and cybersecurity for Canadian construction companies with 10 to 150 employees — CISSP-certified security leadership, services aligned to CIS Controls v8.1, and a team that understands the pace and pressure of construction work.
Cybersecurity Threats Targeting Construction Companies
Ransomware & Project Shutdowns
Construction companies depend on project management, estimating, accounting, and file-sharing systems to keep jobs moving. Ransomware locks these tools and halts coordination across every active project. Even a short outage delays bids, disrupts schedules, and creates downstream problems with owners, subcontractors, and suppliers.
Phishing & Wire Fraud
Attackers impersonate suppliers, subcontractors, or project owners to redirect payments or deliver malware. Construction payment chains involve multiple parties, progress draws, and time pressure — exactly the conditions wire fraud and business email compromise thrive in.
Multi-Site & Field Exposure
Construction crews work from job sites, vehicles, and temporary offices with varying connectivity and security. Unmanaged laptops, personal devices, and unsecured Wi-Fi create entry points that office-only IT models do not address.
Subcontractor & Vendor Access Risk
Construction firms share plans, portals, and project data with subcontractors, architects, engineers, and suppliers. If outside credentials are compromised or stale access is left in place, attackers enter through a partner relationship rather than a direct attack.
Why Canadian Construction Companies Choose Fusion
Construction creates IT demands that generic office-focused providers underestimate. Project schedules depend on estimating, accounting, and project management systems staying available. Field operations add mobile devices, remote access, multi-site connectivity, and subcontractor coordination that require tighter operational control than a standard office.
Fusion has supported Canadian businesses where uptime, security, and accountability matter since 2012. Our CEO holds the CISSP certification — your security posture is guided by senior cybersecurity leadership, not a generalist help desk. We align services to CIS Controls v8.1, giving your business a defensible baseline for insurance applications, vendor questionnaires, and day-to-day control hygiene.
93%
First-call resolution rate
1 Hour
Target on critical issues
14 Years
Serving Canadian businesses
CISSP
Certified security leadership
Managed IT Services for Construction Companies
Help Desk & Day-to-Day Support
When a project manager cannot access the estimating platform, a field laptop fails before a bid deadline, or the office network drops — one call, one technician who already knows your environment. 93% resolved on the first call.
Multi-Site Connectivity
Construction companies operate from a head office, satellite offices, and rotating job sites. Fusion provides secure remote access, site-to-site VPN, cloud connectivity, and network infrastructure that keeps your teams connected regardless of location.
Mobile Device Management
Field crews use phones, tablets, and laptops across job sites with varying connectivity. Fusion manages device configuration, security policies, application deployment, and remote wipe capabilities so your mobile fleet is controlled and protected.
Construction Software Support
We support the IT infrastructure your construction software depends on — workstations, servers, networking, backups, identity, Microsoft 365, and user access. We coordinate with your software vendors for application-layer issues while keeping the underlying environment stable and secure.
Cybersecurity & Threat Monitoring
Endpoint protection, MDR through Huntress, email security, vulnerability management, MFA, backup oversight, and response coordination. The goal: stop a compromised device or identity from becoming a company-wide outage.
Backup & Disaster Recovery
Encrypted, air-gapped backups with tested restores. Not just software installed in the background — actual recovery readiness so project files, financial data, bid history, and business records can be recovered cleanly under pressure.
IT That Scales When You Win New Work
Construction companies experience sharp growth bursts when new contracts land. Ten new hires need laptops provisioned, accounts created, security configured, and access to project management systems — often within days, not weeks. When a project wraps, those accounts need to be offboarded cleanly with access revoked and data secured. Fusion handles onboarding and offboarding at the pace construction demands, so your team focuses on building instead of wrestling with IT logistics.
Security, Insurance, and Compliance Considerations
Privacy Obligations
This content is informational and does not constitute legal advice. Construction companies handle employee records, payroll data, customer information, and subcontractor data. Depending on your activities and jurisdiction, your business may be subject to PIPEDA and/or provincial privacy obligations. Where a breach creates a real risk of significant harm, businesses may need to report it, notify affected individuals, and keep breach records for at least two years. Fusion’s incident response processes, documentation discipline, and security controls support that operational readiness.
Cyber Insurance & Bonding
Cyber insurers increasingly expect documented controls around MFA, backups, endpoint protection, email security, and incident response. A structured baseline makes renewals, underwriting conversations, and bonding applications easier. Construction firms bidding on larger projects or public contracts may face cybersecurity requirements as part of the qualification process.
CyberSecure Canada
CyberSecure Canada is a federal certification program designed to help small and medium-sized businesses demonstrate baseline cybersecurity practices. Fusion’s CIS Controls v8.1 alignment maps to the 13 control areas CyberSecure Canada evaluates, helping construction firms build toward certification readiness if they choose to pursue it.
What Fusion Clients Say
We went from 35 employees to 70 in under a year after landing two major contracts. Every new hire needed a laptop provisioned, accounts set up, security configured, and access to our project management stack — usually within 48 hours. Fusion handled every single onboarding without us having to micromanage it. That kind of responsiveness let us focus on growth instead of wrestling with IT logistics.
I got the call no business owner wants — our systems were locked and there was a ransom demand on every screen. I called Fusion at 9pm on a Friday. They had someone working on it within the hour. By Monday morning our team walked in and got back to work like nothing happened. Every file recovered. No ransom paid.
We run four active job sites at any given time and our old IT provider treated us like a small office. Fusion understood from day one that our people are spread across locations and need reliable access to plans, schedules, and documents from the field. The difference was immediate.
Frequently Asked Questions
What IT support do construction companies need?
Reliable help desk, Microsoft 365 management, secure backups, endpoint protection, patch management, identity and access control, mobile device management, and support for the IT systems that project management, estimating, and accounting software depend on. Companies with field crews and multiple job sites also need remote access, VPN, and mobile device policies.
How do you support construction teams working from job sites?
Secure remote access, cloud-based collaboration through Microsoft 365, mobile device management for phones and tablets, VPN for site-to-site connectivity, and a help desk that understands field conditions. Fusion ensures your crews can access plans, schedules, and documents from anywhere with an internet connection.
How much does managed IT cost for a construction company in Canada?
Pricing depends on user count, sites, device complexity, security requirements, and support scope. Fusion prices managed IT as a predictable monthly service. Construction companies with multiple locations or tighter security requirements should expect a scoped assessment before pricing.
Can you support our project management and estimating software?
Fusion supports the IT infrastructure your construction software depends on — workstations, servers, backups, networking, security, and user access. For vendor-specific application issues, we coordinate with the software vendor while maintaining the surrounding environment.
What happens if ransomware hits during an active project?
Immediate triage, containment, and restore from encrypted, air-gapped backups. In a published case study, a client was hit on a Friday evening and was fully operational by Monday morning — 100% data recovered, $0 ransom paid.
How do you handle onboarding when we win a new contract?
Fusion provisions laptops, creates accounts, configures security, sets up access to project management systems, and handles the full IT onboarding process at the pace construction demands. When projects wrap, we offboard cleanly with access revoked and data secured.
How do you help construction firms meet cybersecurity requirements for bids?
Fusion’s CIS Controls v8.1 alignment produces documented evidence of MFA, access controls, backup governance, endpoint protection, vulnerability management, and incident response readiness. This documentation supports prequalification questionnaires, owner audits, and bonding applications.
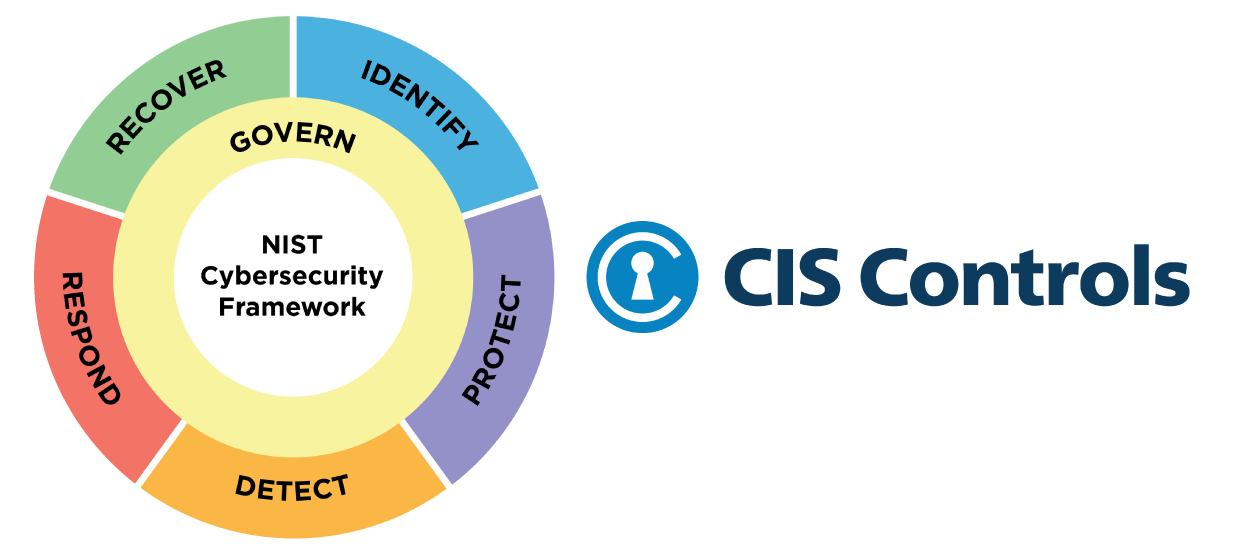
The CIS Critical Security Controls (CIS Controls) are a prescriptive, prioritized, and simplified set of best practices Fusion uses to strengthen your cybersecurity posture. This simplified cybersecurity approach is proven to help you defend against today’s top threats.
Testimonials
Recognized as one of Canada’s 50 Best Managed IT Companies. Verify on e-ChannelNews →




