Network Penetration Testing: A Step-by-Step Guide for Canadian Businesses
By James Mitchell, CISSP | Security Leadership since 2012
Network security penetration testing, often shortened to pen testing, is the process of finding potential security vulnerabilities in networks, systems, and applications by having ethical hackers attempt to break through your cyber defenses using real-world attack techniques. Unlike passive vulnerability scans, pen tests actively exploit weaknesses to show exactly how far an attacker could go and what data they could access.
By Mike Pearlstein, CISSP — Fusion Computing
If you need a scoped engagement instead of general background, review our cybersecurity assessment Toronto page for assessment-led work and our cybersecurity services page for broader managed security coverage.
KEY TAKEAWAYS
- Penetration testing simulates real attacks against your network. Unlike vulnerability scanning, it proves what’s actually exploitable.
- Annual pen tests are the minimum. Test after major infrastructure changes, security incidents, or before launching customer-facing systems.
- PCI-DSS mandates annual pen tests. PIPEDA requires demonstrable safeguards – pen testing proves due diligence.
- The global pen testing market hit US$2.74 billion in 2025 (Fortune Business Insights, 2025) and is projected to reach $7.41 billion by 2034.
TL;DR
Penetration testing simulates real cyberattacks to find vulnerabilities before hackers do. Network pen tests cost $5K–$25K for Canadian SMBs, satisfy compliance requirements (PCI DSS, PIPEDA, cyber insurance), and should run annually at minimum. Fusion Computing provides pen testing as a standalone engagement or within managed cybersecurity packages.
What is network penetration testing?
Network security testing is the process of evaluating a computer network’s defenses by simulating real-world cyberattacks. It includes penetration testing, vulnerability scanning, configuration audits, and firewall rule reviews to identify exploitable weaknesses before attackers do. A professional network security test follows a structured methodology—scoping, reconnaissance, exploitation, and reporting—and delivers prioritized remediation steps.
Network penetration testing is a controlled, authorized cyberattack simulation against an organization’s network infrastructure. It tests firewalls, routers, switches, servers, VPNs, and wireless access points for exploitable vulnerabilities. Pen testing follows a structured methodology: reconnaissance, scanning, exploitation, post-exploitation, and reporting with prioritized remediation steps.
TL;DR
Network penetration testing simulates real-world cyberattacks against your network infrastructure to identify exploitable vulnerabilities before attackers find them. A pen test covers external perimeter testing, internal network testing, wireless testing, and social engineering. Canadian businesses in regulated industries should conduct penetration tests annually and after major infrastructure changes.
Network penetration testing is a controlled security exercise (aligned with the Penetration Testing Execution Standard) where trained professionals simulate real cyberattacks against your network to find exploitable vulnerabilities before malicious actors do. Unlike vulnerability scanning (automated and passive), pen testing is manual and active—testers actually attempt to breach defenses. According to DeepStrike’s 2025 research, manual testing uncovers nearly 2,000 times more unique vulnerabilities than automated scans alone. PCI-DSS mandates annual pen tests; PIPEDA requires demonstrated safeguards.
Pen testing is a structured security exercise—and increasingly offered as managed penetration testing services—where trained professionals simulate real-world attacks to find exploitable vulnerabilities before malicious actors do. A good pen test goes beyond listing vulnerabilities; it demonstrates actual attack paths and business impact. This is critical for Canadian businesses facing increasing threat actors and compliance requirements like PIPEDA and PCI-DSS.
Fusion Computing is a Canadian-owned managed IT and cybersecurity provider serving businesses with 10 to 150 employees since 2012. With a 93% first-contact resolution rate and CISSP-certified security leadership, Fusion Computing delivers monitoring, help desk, and security services aligned to CIS Controls v8.1.
Pen Testing vs. Vulnerability Scanning: Key Differences
Many organizations confuse these two approaches, but they serve different purposes. Vulnerability scanning is automated and passive; pen testing is manual and active. If you’re not sure which you need, the table below will clarify. According to Cyphere’s 2025 pen testing research, in 93% of companies tested, pentesters could breach the internal network perimeter given any foothold—a finding that automated scanners can’t replicate.
| Criterion | Vulnerability Scan | Penetration Test |
|---|---|---|
| Approach | Automated, passive | Manual, active exploitation |
| Time Required | Hours to days | Days to weeks |
| Exploits Vulnerabilities | No — identifies only | Yes — proves real-world impact |
| False Positives | Often high | Minimal — verified findings |
| Reports Attack Chains | No | Yes — shows full breach path |
| Best For | Baseline inventory of issues | Proof of exploitability and impact |
The Four Phases of Network Penetration Testing
A professional pen test follows a structured methodology to ensure thorough, repeatable results. These four phases build on each other to simulate a realistic attack and deliver actionable findings. Each phase has clear objectives, deliverables, and decision points. If you haven’t been through a pen test before, here’s what to expect at every stage.
Phase 1: Scoping and Information Gathering
The first phase establishes the scope, objectives, and boundaries of the test. You’ll define what systems are in and out of scope, the test type (black/grey/white box), whether to exploit findings or report only, and the timeframe. This clarity prevents misunderstandings and ensures the test meets your business goals. Don’t skip this step—it’s what separates a structured engagement from a random scan.
Key activities:
- Review network architecture, asset inventory, and IT documentation
- Identify critical systems and sensitive data locations
- Determine test scope (internal, external, or both)
- Agree on exploitation rules and downtime tolerance
- Set reporting requirements and remediation priorities
Phase 2: Reconnaissance and Mapping
Testers now map the target environment using port scanners, DNS enumeration, and open-source intelligence (OSINT) to discover hosts, services, applications, and potential entry points. This is where attackers typically spend the most time—mapping defenses before striking. You won’t see much happening during this phase, but it’s laying the groundwork for everything that follows.
Key activities:
- Perform network scans to identify active hosts and listening ports
- Enumerate services and determine software versions
- Research public information about the organization (DNS, WHOIS, social media)
- Identify third-party integrations and supply chain connections
- Document all findings for prioritization in Phase 3
Phase 3: Active Exploitation and Testing
With the environment mapped, testers now attempt to breach defenses using discovered vulnerabilities. This may include leveraging weak credentials, unpatched systems, misconfigurations, or social engineering—whatever a real attacker would use. Detailed notes are kept on each attempt, method, and outcome to build the attack narrative. It’s not unusual for a single overlooked misconfiguration to give an attacker full domain access.
Key activities:
- Attempt to exploit identified vulnerabilities with real-world attack techniques
- Chain vulnerabilities together to access sensitive systems or data
- Conduct social engineering (phishing, pretexting) if in scope
- Test internal controls once external access is gained
- Document successful attack paths and data exposure
Phase 4: Reporting and Remediation Planning
Testers compile findings into a formal report with risk ratings, evidence of exploitation, business impact, and step-by-step remediation guidance. This report becomes your roadmap for closing security gaps and often serves as evidence of due diligence to regulators, auditors, and cyber insurance underwriters. If your report doesn’t include specific fix instructions, it isn’t worth much.
Key deliverables:
- Executive summary with risk overview and business impact
- Detailed vulnerability descriptions and proof of exploitation
- Prioritized remediation steps with timelines
- Re-testing plan to verify fixes are effective
- Ongoing testing recommendations and frequency
Get a Pen Test Scoping Assessment
Network Penetration Testing Methodology: PTES and NIST SP 800-115
Professional pen testers follow established methodologies rather than ad hoc approaches. The quality difference between a rigorous test and a checkbox exercise comes down almost entirely to which standard the team actually works from. You shouldn’t have to guess—ask your provider directly.
PTES: Penetration Testing Execution Standard
PTES is the most widely referenced pen testing methodology in the industry. It defines seven phases: pre-engagement interactions, intelligence gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting. For network pen testing, the exploitation and post-exploitation phases are where a quality test separates from a vulnerability scan. A real tester proves exploitability and lateral movement potential, not just a list of CVEs. You can’t assess your true risk without this step.
NIST SP 800-115: Technical Guide to Information Security Testing
Published by the National Institute of Standards and Technology, SP 800-115 provides a technical framework for security testing across four phases: planning, discovery, attack, and reporting. The NIST model is particularly relevant when your clients or contracts reference federal information security standards. Canadian businesses selling to U.S. federal agencies or operating under NIST Cybersecurity Framework requirements should ensure their pen testing provider can map findings to this standard.
CIS Controls v8.1: Control 18: Penetration Testing
CIS Control 18 defines the program-level requirements for pen testing. Safeguard 18.1 requires establishing a documented pen testing program; 18.2 requires annual external network pen tests; 18.3 requires evidence of remediation and re-testing. Fusion aligns all network pen testing engagements to CIS Controls v8.1, which gives clients documentation that satisfies most compliance auditors and cyber insurance underwriters. If your provider can’t demonstrate CIS alignment, that’s a red flag.
When evaluating providers, ask which methodology they follow and how their report maps to it. A provider who can’t answer that question clearly is running a scan with a pen testing price tag.
Network Penetration Testing Methodology: A Practical Step-by-Step Approach
Most network pen testing methodologies describe what happens in abstract phases. This is what the work actually looks like at each stage—including the specific techniques a qualified tester uses and what each step is designed to find.
Stage 1: Scoping and target definition
Before any testing begins, scope is defined in writing: IP ranges, subnets, specific hosts, and anything explicitly out of scope. For a typical Canadian SMB engagement this includes on-premises network infrastructure, VPN termination points, DMZ segments, and cloud-connected gateways. The scope document becomes the authorization that protects both parties. Without it, the tester doesn’t have legal standing to probe systems even if the client verbally agreed.
Key outputs: signed rules of engagement, IP scope list, out-of-scope exclusions, emergency contact protocol for if a critical system is disrupted during testing.
Stage 2: Passive and active reconnaissance
Passive reconnaissance collects information without touching the target network: DNS records, WHOIS data, public certificate transparency logs, BGP routing, and services visible from the internet. Tools like Shodan and Censys reveal what the organization has inadvertently exposed publicly—often more than they realize.
Active reconnaissance begins network contact: ICMP sweeps to discover live hosts, TCP/UDP port scans (nmap is the standard starting point), OS fingerprinting, and service version detection. For a network with 200 hosts, this stage maps every live device, its open ports, and the service versions running on each. That version data feeds directly into the vulnerability identification stage.
Stage 3: Vulnerability identification and threat modeling
Service version data from reconnaissance gets cross-referenced against known vulnerabilities. This isn’t a vulnerability scan: it’s a manual and automated analysis of which discovered services are actually exploitable in the current environment. A CVE affecting an Apache version may be critical on a public-facing server and irrelevant on an air-gapped internal system. Context determines priority. According to Edgescan’s 2025 Vulnerability Statistics Report, over 21,500 new CVEs were disclosed in the first half of 2025 alone—an 18% jump over the same period the year prior.
Threat modeling maps the likely attack paths: where does an external attacker land first (typically a perimeter device or VPN endpoint), what can they reach from that initial foothold, and what’s the highest-value target reachable through lateral movement? This stage determines which vulnerabilities get exploited in Stage 4 and in what order.
Stage 4: Active exploitation and lateral movement testing
This is where a network pen test diverges entirely from a vulnerability scan. The tester attempts to exploit confirmed vulnerabilities, pivot between network segments, escalate privileges, and reach sensitive systems. For a network engagement, this typically includes:
- Segmentation testing: verifying that VLANs and firewall rules actually prevent lateral movement between segments (workstations, servers, management networks, OT/IoT where applicable)
- Credential attacks: default credentials on network devices, password spraying against Active Directory, Pass-the-Hash and Kerberoasting where domain access exists
- LAN-layer protocol attacks: SMB relay, LLMNR/NBT-NS poisoning, ARP spoofing—techniques that external scanners never test and that are common in real-world breaches
- Service exploitation: proving exploitability of unpatched services with documented proof-of-concept, not just a CVE reference
All findings are logged with evidence: screenshots, packet captures, tool output. This documentation is what lets remediation teams reproduce and verify each finding independently.
Stage 5: Post-exploitation and impact assessment
After a foothold is established, the tester documents what an attacker could access from that position: which data stores are reachable, what systems can be pivoted to, what credentials can be harvested or re-used. The goal isn’t to cause damage—it’s to demonstrate the realistic blast radius of a successful breach. This answers the question executives actually need answered: if someone gets in, what do they get?
Stage 6: Remediation-focused reporting
The deliverable that separates a quality engagement from a checkbox exercise is the report. Each finding should include: a severity rating with CVSS score, the affected host and service, an exact exploitation path with reproduction steps, the business risk in plain language, and a specific remediation recommendation. Vague recommendations like “update your systems” aren’t actionable; a good report names the exact patch, configuration change, or architectural fix required.
Most qualified providers include a re-test at 30–60 days to verify critical findings were remediated. Ask for this as part of your engagement scope. It’s the only way to confirm the risk is actually closed, not just addressed on paper.
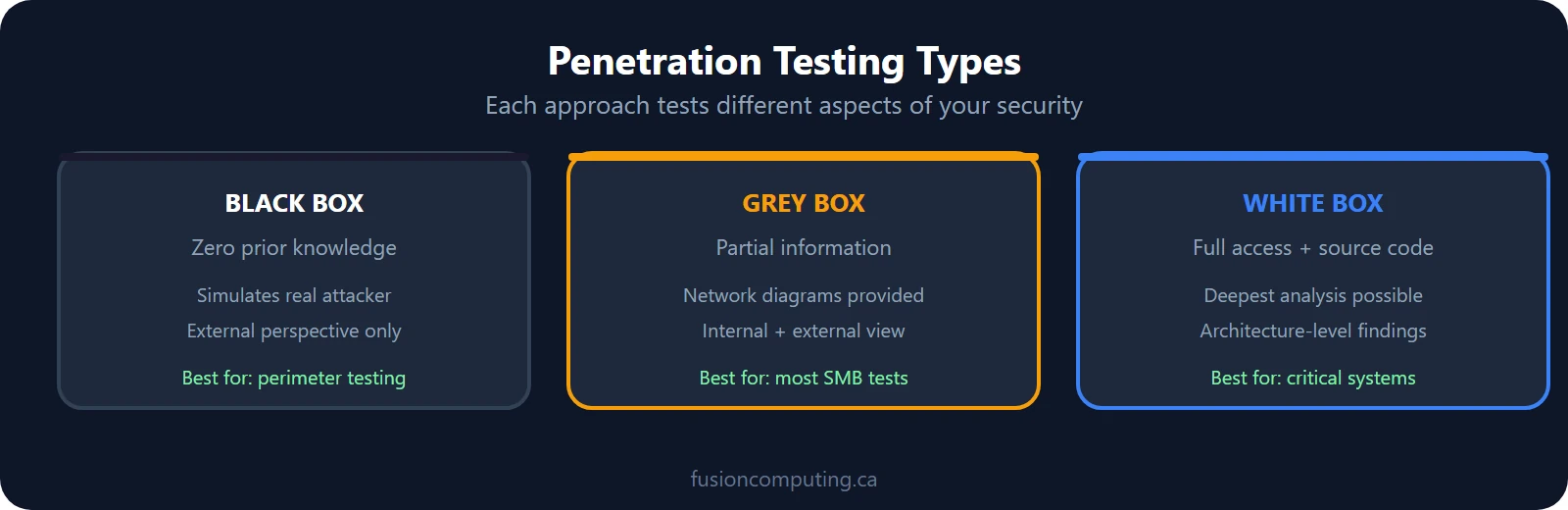
Types of Penetration Tests: Black, Grey, and White Box
The test type determines how much information testers start with, which directly affects what they can find and how realistic the simulation is. Choose based on your risk tolerance and what you want to learn. If you aren’t sure which type fits your situation, here’s a quick breakdown.
Black box testing: Testers begin with zero knowledge of your environment and attack from outside. This simulates a true external attacker and is valuable for testing perimeter defenses, but it can miss internal vulnerabilities if external entry fails. It’s the most realistic approach for simulating real-world threats.
Grey box testing: Testers have partial access (e.g., a standard user account or network diagram). This balances realism with depth—they avoid wasting time on reconnaissance but still have to work through controls. It’s ideal for finding internal vulnerabilities after an external breach.
White box testing: Testers have full access to source code, architecture documentation, and credentials. This finds the most vulnerabilities and architectural flaws, but it’s the least realistic. Best for post-acquisition reviews or secure code assessments. Usually it’s also the most time-consuming.
How Often Should You Test?
A network penetration test typically takes 1 to 3 weeks from scoping to final report delivery. The active testing phase is usually 3 to 7 business days, depending on the number of IP addresses, network segments, and whether internal, external, or both scopes are included. Larger or more complex environments with multiple locations may require additional time.
Most security frameworks recommend annual pen tests at minimum, plus testing after major changes. Compliance mandates and risk appetite drive your testing frequency. Canadian businesses in regulated industries have stricter requirements than those in less-regulated sectors. Over 70% of organizations have adopted PTaaS in some form (Strobes, 2025), with another 14% planning to—reflecting a shift away from annual-only testing.
Testing triggers include:
- Annual baseline — minimum for most organizations
- Major infrastructure or application deployment
- After a security incident or breach
- Before launching customer-facing or payment systems
- Compliance requirement (PCI-DSS every two years at minimum; PIPEDA as risk-based)
- Supply chain changes or new third-party integrations
Organizations with mature security programs often test twice per year. Those in high-risk sectors (finance, healthcare, utilities) may test quarterly or conduct continuous red team exercises.
What compliance standards require penetration testing?
Regulatory frameworks increasingly mandate penetration testing and broader cybersecurity testing services as proof of due diligence. PIPEDA requires organizations to implement safeguards proportional to risk; PCI-DSS mandates testing for payment card processors; and industry standards like ISO 27001 expect it. Pen testing also strengthens your position with cyber insurance carriers. According to Cobalt’s 2025 compliance research, PCI-DSS service providers now face biannual segmentation testing requirements on top of annual pen tests.
Key compliance frameworks:
- PIPEDA (Personal Information Protection and Electronic Documents Act): Requires demonstration of appropriate security safeguards; pen testing proves you’re taking this seriously.
- PCI-DSS (Payment Card Industry Data Security Standard): Level 1 merchants must conduct or receive an external pen test annually; Level 2–4 annually or after network changes.
- NIST Cybersecurity Framework: Includes assessment and penetration testing as core practices for detecting and responding to threats.
- CIS Controls v8.1: Emphasizes testing controls through attack simulation; pen testing directly supports Control 18 (Penetration Testing).
- ISO 27001: Expects regular security testing including penetration testing as part of your information security management system.
| Framework | Pen Test Required? | Minimum Frequency | Scope |
|---|---|---|---|
| PCI-DSS | Yes (mandatory) | Annual + after changes | External and internal; segmentation testing biannual for SPs |
| PIPEDA | Implied (risk-based) | Annual recommended | Systems handling personal information |
| HIPAA | Strongly recommended | Annual (proposed mandatory) | ePHI systems and access controls |
| SOC 2 | Recommended (not explicit) | Annual | Trust Services Criteria controls |
| ISO 27001 | Recommended | Annual | ISMS scope; risk-based determination |
| CIS Controls v8.1 | Yes (Control 18) | Annual | External network; remediation re-test |
What should a quality pen test report include?
A strong pen test report isn’t just a list of findings—it’s a business-aligned action plan. It quantifies risk, explains attack chains, and provides step-by-step fixes that your IT team can execute immediately. If you’re getting a report that’s mostly scanner output, you’re not getting a real pen test.
A quality report should have:
- Executive Summary: One-page risk overview, remediation timeline, and business impact
- Scope and Methodology: What was tested, how, and any limitations
- Risk Rating Matrix: Clear, consistent severity levels tied to CVSS scores
- Vulnerability Descriptions: Proof of exploitation, not just theoretical issues
- Attack Chains: How multiple weaknesses were chained to reach sensitive data
- Remediation Steps: Specific, actionable fixes (e.g., patch version X, update policy Y)
- Proof of Concept Code: If complex exploitation method, include sample code or screenshots
- Re-testing Plan: Timeline and scope for verifying fixes
Fusion Computing serves businesses across Toronto & GTA | Hamilton | Metro Vancouver
Penetration Testing Services: What to Look For
When evaluating penetration testing services, look beyond price and focus on methodology, credentials, and reporting quality. A quality penetration testing service should follow recognized frameworks (PTES, OWASP, NIST SP 800-115), employ CISSP or OSCP-certified testers, and deliver reports that translate technical findings into business risk. You won’t get that from a firm that treats pen testing as a commodity product.
Many Canadian organizations now treat penetration testing as a service (PTaaS)—an ongoing engagement model where testing is conducted continuously or on a regular cadence rather than as a one-time project. This approach provides consistent security validation and it’s particularly valuable for businesses with frequent infrastructure changes or compliance obligations that require regular testing cycles.
When comparing a penetration test service to an in-house effort, consider that external testers bring fresh perspective and specialized tooling that internal teams rarely maintain. A dedicated penetration test as a service provider can scale testing across multiple environments (cloud, on-premises, hybrid) while maintaining independence from your operations team—a requirement for many compliance frameworks.
Key criteria for choosing cybersecurity testing services:
- Industry certifications (CISSP, OSCP, CEH) and verifiable experience
- Methodology aligned with PTES, OWASP, or NIST standards
- Clear scoping process with written rules of engagement
- Reports that include business impact, not just CVSS scores
- Re-testing included to verify remediation effectiveness
- Canadian data residency and PIPEDA compliance awareness
The Role of Managed IT Service Providers in Penetration Testing
Many Canadian MSPs now offer or partner with dedicated penetration test services firms to help clients meet compliance and reduce breach risk. A CISSP-certified MSP can advise on testing frequency, help interpret findings, and coordinate remediation with your internal team. Fusion Computing’s CISSP-led security team has conducted thousands of pen tests since 2012, making us a trusted partner for Canadian businesses. If you don’t have internal security expertise, working with an MSP can simplify the entire process.
If you lack internal security expertise, an MSP can manage the entire process: scoping the test, coordinating with the testers, prioritizing findings, and re-testing to confirm fixes. This takes the burden off your IT staff and ensures consistency across testing cycles.
Penetration Test as a Service (PTaaS): What It Costs and How It Works
Penetration test as a service (PTaaS) delivers continuous or on-demand penetration testing through a managed provider, replacing the traditional model of hiring a one-off consultant for an annual engagement. For Canadian businesses, PTaaS typically costs CA$5,000–$25,000 annually depending on scope, compared to CA$10,000–$50,000 for a single traditional engagement. According to Bright Defense’s 2026 pricing guide, most vendors price pen tests using a day rate of $1,000–$3,000 per tester day, with enterprise-grade continuous testing platforms running $75K–$150K+ annually.
What makes PTaaS different from traditional pen testing:
- Continuous testing: Not just once a year. PTaaS platforms test on a recurring schedule, catching new vulnerabilities as your environment changes.
- Faster remediation: Findings are reported in real time through a portal, not in a PDF delivered 6 weeks after the test.
- Compliance alignment: PTaaS satisfies PCI DSS, PIPEDA, and cyber insurance requirements for regular penetration testing.
- Scope flexibility: Test external perimeter, internal network, web applications, or all three on different cadences.
Fusion provides penetration test services as part of our managed cybersecurity program or as a standalone engagement. Every test is conducted by certified professionals following the PTES methodology, with a detailed report including remediation priorities mapped to your risk profile.
Not Sure Where Your IT Stands?
Our free IT assessment gives you a clear picture of your infrastructure, security gaps, and opportunities. No obligation, no sales pressure.
Related Resources
Ready to Test Your Network Security?
A pen test report is only useful if you’ve got a plan to act on it. Fusion Computing’s CISSP-certified team offers network security testing and cybersecurity assessments for Canadian businesses—with clear findings and a remediation roadmap, not just a raw vulnerability list.
What is network penetration testing?
Network penetration testing is a structured security exercise where trained professionals attempt to break through your cyber defenses using the same techniques real attackers use. The goal is to find exploitable vulnerabilities before malicious actors do. Unlike vulnerability scanning, pen testing actively exploits weaknesses to show exactly how far an attacker could get and what data they could access.
What are the four main steps of a network pen test?
A pen test typically follows four phases: scoping and information gathering (define goals and boundaries), reconnaissance (map the target environment), active exploitation (attempt to breach defenses), and reporting (document findings and remediation steps). Each phase builds on the previous one to give a realistic picture of attacker capabilities and business impact.
How is pen testing different from vulnerability scanning?
Vulnerability scanning is automated and passive, flagging known weaknesses without trying to exploit them. Pen testing is manual and active, with skilled professionals actually attempting to break in. Scanning gives you a broad view of potential issues; pen testing shows you which of those issues are genuinely exploitable and what the real-world impact of a breach would be.
How often should a business conduct a penetration test?
Most security frameworks recommend annual pen tests at minimum. Businesses should also conduct one after significant infrastructure changes, after a security incident, or before launching new customer-facing applications. Companies in regulated industries like finance or healthcare often require semi-annual pen tests as part of compliance obligations. Mature security programs may test twice yearly or conduct continuous red team exercises.
What is the difference between a black box and white box pen test?
In a black box test, testers have no prior knowledge of your environment and start the same way an external attacker would. In a white box test, testers are given full access to documentation, architecture diagrams, and source code. Grey box testing falls in between, providing partial information. Each approach has value; black box tests simulate real attackers, while white box tests find deeper architectural flaws.
What compliance standards require penetration testing?
PCI-DSS mandates annual pen tests for merchants processing payment cards. PIPEDA requires demonstration of safeguards proportional to risk; pen testing proves due diligence. NIST Cybersecurity Framework and CIS Controls v8.1 emphasize testing controls through attack simulation. ISO 27001 expects regular security testing as part of your information security management system. Your industry and the data you hold will determine which standards apply.
What happens after a pen test is complete?
After testing, you receive a detailed report listing every vulnerability exploited, the attack path used, the potential business impact, and specific remediation steps. Your IT team works through the findings by priority, applying patches and configuration changes. A re-test confirms the fixes are effective. The completed report is valuable documentation for cyber insurance underwriters and compliance auditors. Many organizations track remediation progress and schedule follow-up testing within 30–90 days.
What is penetration testing as a service (PTaaS)?
Penetration testing as a service (PTaaS) is an ongoing engagement model where a penetration test service provider conducts continuous or regularly scheduled testing rather than a one-time assessment. PTaaS gives businesses consistent security validation, faster vulnerability discovery, and is well-suited for organizations with frequent infrastructure changes or strict compliance requirements like PCI-DSS and PIPEDA.
Fusion Computing serves Canadian businesses across:
Cybersecurity Services: Toronto · Cybersecurity Services: Hamilton · Cybersecurity Services: Vancouver
Network Penetration Testing for Canadian Businesses
Fusion Computing offers CISSP-certified penetration testing, vulnerability assessments, and remediation planning. Our team has secured Canadian organizations since 2012, with zero breaches at client sites.
External References:
Related Resources
- OWASP Web Security Testing Guide — Industry-standard methodology for web and application testing
- NIST SP 800-115 Technical Security Testing and Assessment — Federal standards for penetration testing practices
- Canadian Centre for Cyber Security Tools and Services — Government guidance on cybersecurity testing
- Fortune Business Insights: Penetration Testing Market 2025 — Global market size and growth projections
- DeepStrike: Penetration Testing Statistics 2025 — 86 key pen testing statistics, trends, and takeaways
- Edgescan: 2025 Vulnerability Statistics Report — Annual vulnerability landscape and CVE data
- Cobalt: Penetration Testing Compliance Requirements 2025 — Framework-by-framework compliance analysis
Last reviewed: April 2026. Fusion Computing